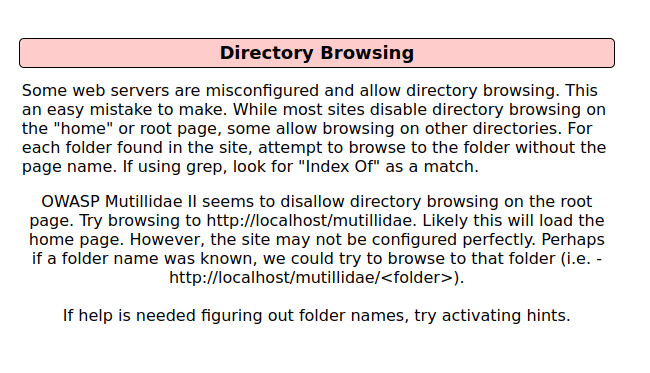
In this walk through, we will be going through the Directory Browsing vulnerability section from Mutillidae Labs. We will be exploring and exploiting Directory Browsing and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.
Table of Contents
Security Level: 0 (Hosed)
- Setting the security level to 0 or Hosed.

- In this challenge we have to used directory browsing to get sensitive directories.
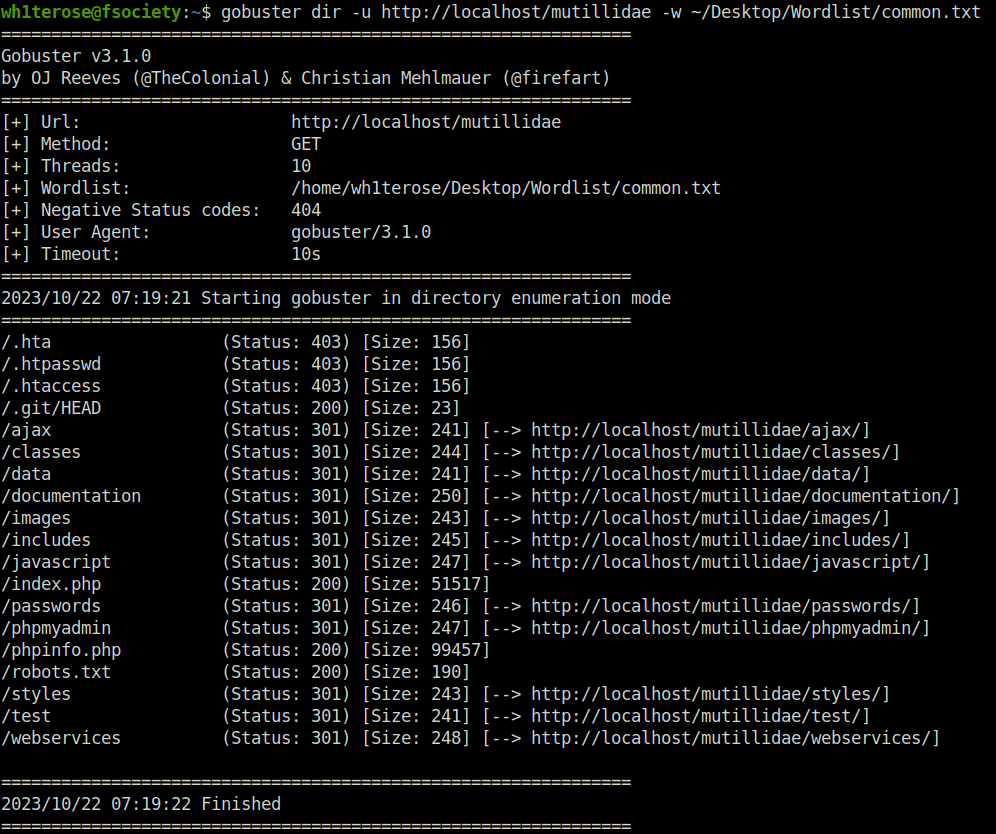
- I used gobuster for directory bruteforcing.
gobuster dir -u http://localhost/mutillidae -w ~/Desktop/Wordlist/common.txt
Also Read: Mutillidae – Client-side Control Challenge
Conclusion:

So, we finally completed all the security levels for the Directory Browsing Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Next, we can mitigate the potential attack by limiting the directory bruteforcing and disallowing direct access to the directories via browser. On that note, i will take your leave and will meet you in next one with another Mutillidae vulnerability writeup, till then “Keep Hacking”.




