In this walk through, we will be going through the Insecure Direct Object Reference (LFI) vulnerability section from Mutillidae Labs. We will be exploring and exploiting Insecure Direct Object Reference (IDOR LFI) and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.
Table of Contents
Security Level: 0 (Hosed)
- Setting the security level to 0 or Hosed.

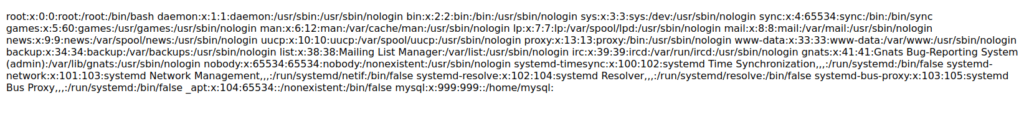
- In this challenge, we have to perform LFI by reading the contents of a file on the system.
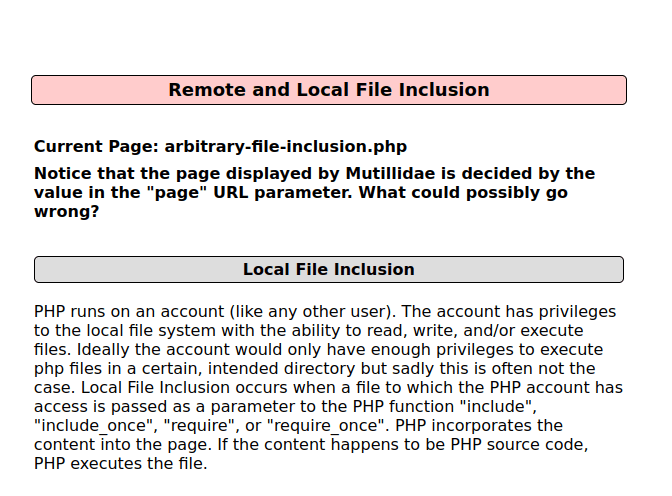
- I used the below payload to read the contents of the /etc/passwd file.
http://localhost/mutillidae/index.php?page=../../../../../etc/passwd

Also Read: Mutillidae – HTML Injection via HTTP Headers (Site Footer)
Conclusion:

So, we finally completed all the security levels for the Insecure Direct Object Reference (LFI) Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Next, we can mitigate the potential IDOR attacks by implementing access control checks for each object that users are trying to access. The Web frameworks often provide ways to facilitate this. Along with that, avoid exposing identifiers in URLs and GET bodies if possible. Instead, determine the currently authenticated user from session information. Also, LFI can be mitigated by disabling “allow_url_include” and “allow_url_fopen” in PHP configuration files and sanitizing the user input.On that note, i will take your leave and will meet you in next one with another Mutillidae vulnerability writeup, till then “Keep Hacking”.