In this walk through, we will be going through the Nmap room from Tryhackme. After completing this room, you will be able to perform network scans on the targets using one of the most popular tool called Nmap. So, let’s get started.

What is Nmap ?
Nmap stands for Network Mapper. It is a network scanning tool which is used to find live hosts, open ports, version of the running services, OS and other useful information. It is used heavily to find potential paths to get into the system. It is also used for vulnerability scanning with its NSE Scripting Engine.
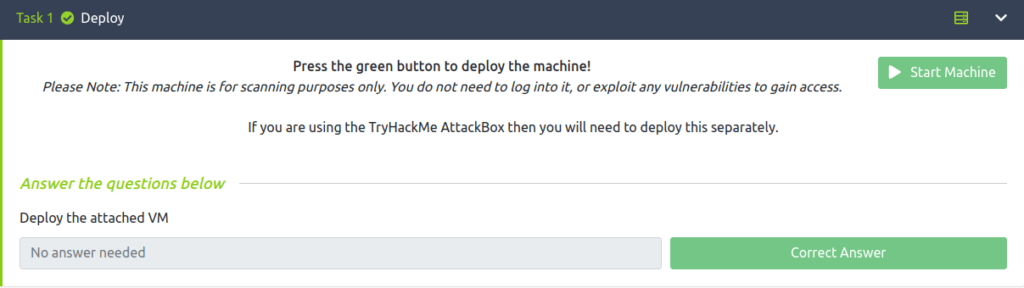
Task 1 – Deploy
Deploy the attached VM to get started with the target.
Task 2 – Introduction
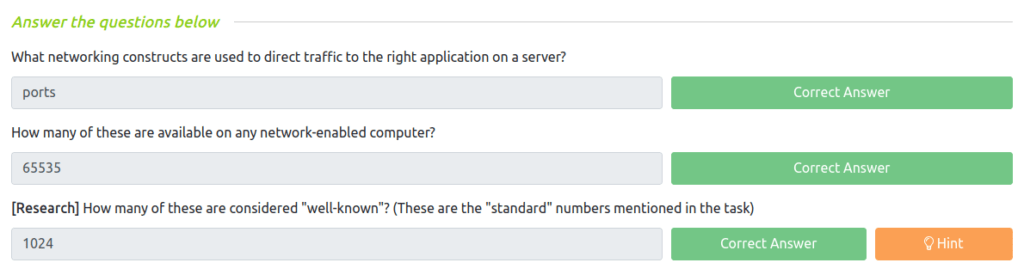
Question 1 – What networking constructs are used to direct traffic to the right application on a server?
Ports
Question 2 – How many of these are available on any network-enabled computer?
65535
Question 3 – [Research] How many of these are considered “well-known”? (These are the “standard” numbers mentioned in the task)
1024
Task 3 – Nmap Switches
Question 1 – What is the first switch listed in the help menu for a ‘Syn Scan’ (more on this later!)?
-sS
Question 2 – Which switch would you use for a “UDP scan”?
-sU
Question 3 – If you wanted to detect which operating system the target is running on, which switch would you use?
-O
Question 4 – Nmap provides a switch to detect the version of the services running on the target. What is this switch?
-sV
Question 5 – The default output provided by nmap often does not provide enough information for a pentester. How would you increase the verbosity?
-v
Question 6 – Verbosity level one is good, but verbosity level two is better! How would you set the verbosity level to two?
-vv
Question 7 – What switch would you use to save the nmap results in three major formats?
-oA
Question 8 – What switch would you use to save the nmap results in a “normal” format?
-oN
Question 9 – A very useful output format: how would you save results in a “grepable” format?
-oG
Question 10 – Sometimes the results we’re getting just aren’t enough. If we don’t care about how loud we are, we can enable “aggressive” mode. This is a shorthand switch that activates service detection, operating system detection, a traceroute and common script scanning. How would you activate this setting?
-A
Question 11 – How would you set the timing template to level 5?
-T5
Question 12 – How would you tell nmap to only scan port 80?
-p 80
Question 13 – How would you tell nmap to scan ports 1000-1500?
-p 1000-1500
Question 14 – How would you tell nmap to scan all ports?
-p-
Question 15 – How would you activate a script from the nmap scripting library (lots more on this later!)?
--script
Question 16 – How would you activate all of the scripts in the “vuln” category?
--script=vuln



Task 4 – [Scan Types] Overview
![Tryhackme - Nmap Task 4 - [Scan Types] Overview](https://inventyourshit.com/wp-content/uploads/2022/12/Pasted-image-20221005230454-1024x133.png)
Task 5 – [Scan Types] TCP Connect Scans
Question 1 – Which RFC defines the appropriate behavior for the TCP protocol?
RFC 793
Question 2 – If a port is closed, which flag should the server send back to indicate this?
RST
![Tryhackme - Nmap Task 5 - [Scan Types] TCP Connect Scans](https://inventyourshit.com/wp-content/uploads/2022/12/Pasted-image-20221005231802-1024x204.png)
Task 6 – [Scan Types] SYN Scans
Question 1 – There are two other names for a SYN scan, what are they?
Half-Open, Stealth
Question 2 – Can Nmap use a SYN scan without Sudo permissions (Y/N)?
N
![Tryhackme - Nmap Task 6 - [Scan Types] SYN Scans](https://inventyourshit.com/wp-content/uploads/2022/12/Pasted-image-20221005232555-1024x205.png)
Task 7 – [Scan Types] UDP Scans
Question 1 – If a UDP port doesn’t respond to an Nmap scan, what will it be marked as?
open|filtered
Question 2 – When a UDP port is closed, by convention the target should send back a “port unreachable” message. Which protocol would it use to do so?
ICMP
![Tryhackme - Nmap Task 7 - [Scan Types] UDP Scans](https://inventyourshit.com/wp-content/uploads/2022/12/Pasted-image-20221005233032-1-1024x197.png)
Task 8 – [Scan Types] NULL, FIN and Xmas
Question 1 – Which of the three shown scan types uses the URG flag?
xmas
Question 2 – Why are NULL, FIN and Xmas scans generally used?
Firewall Evasion
Question 3 – Which common OS may respond to a NULL, FIN or Xmas scan with a RST for every port?
Microsoft Windows
![Tryhackme - Nmap Task 8 - [Scan Types] NULL, FIN and Xmas](https://inventyourshit.com/wp-content/uploads/2022/12/Pasted-image-20221005233818-1024x278.png)
Task 9 – [Scan Types] ICMP Network Scanning
Question 1 – How would you perform a ping sweep on the 172.16.x.x network (Netmask: 255.255.0.0) using Nmap? (CIDR notation)
nmap -sn 172.16.0.0/16
![Tryhackme - Nmap Task 9 - [Scan Types] ICMP Network Scanning](https://inventyourshit.com/wp-content/uploads/2022/12/Pasted-image-20221005234305-1024x142.png)
Task 10 – [NSE Scripts] Overview
Question 1 – What language are NSE scripts written in?
Lua
Question 2 – Which category of scripts would be a very bad idea to run in a production environment?
intrusive
![Tryhackme - Nmap Task 10 - [NSE Scripts] Overview](https://inventyourshit.com/wp-content/uploads/2022/12/Pasted-image-20221005234722-1024x209.png)
Task 11 – [NSE Scripts] Working with the NSE
Question 1 – What optional argument can the ftp-anon.nse script take?
maxlist
![Tryhackme - Nmap Task 11 - [NSE Scripts] Working with the NSE](https://inventyourshit.com/wp-content/uploads/2022/12/Pasted-image-20221005235347-1024x135.png)
Task 12 – [NSE Scripts] Searching for Scripts
Question 1 – Search for “smb” scripts in the /usr/share/nmap/scripts/ directory using either of the demonstrated methods. What is the filename of the script which determines the underlying OS of the SMB server?

smb-os-discovery.nse
Question 2 – Read through this script. What does it depend on?

smb-brute
![Tryhackme - Nmap Task 12 - [NSE Scripts] Searching for Scripts](https://inventyourshit.com/wp-content/uploads/2022/12/Pasted-image-20221006000158-1024x234.png)
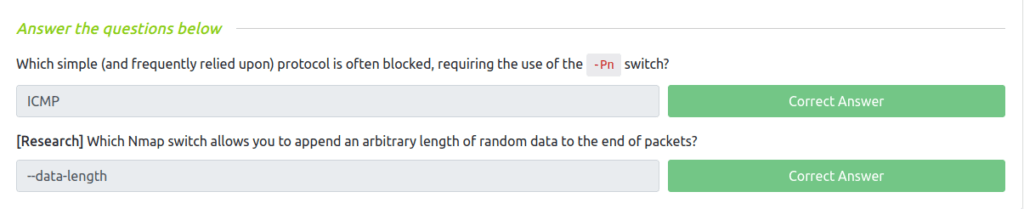
Task 13 – Firewall Evasion
Question 1 – Which simple (and frequently relied upon) protocol is often blocked, requiring the use of the -Pn switch?
ICMP
Question 2 – [Research] Which Nmap switch allows you to append an arbitrary length of random data to the end of packets?
--data-length
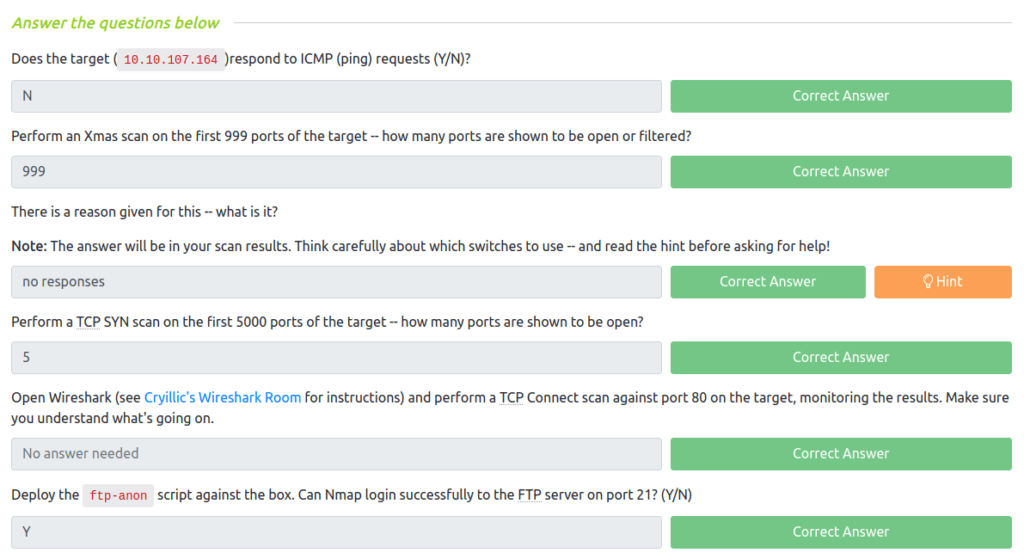
Task 14 – Practical
Question 1 – Does the target (MACHINE_IP)respond to ICMP (ping) requests (Y/N)?

N
Question 2 – Perform an Xmas scan on the first 999 ports of the target — how many ports are shown to be open or filtered?
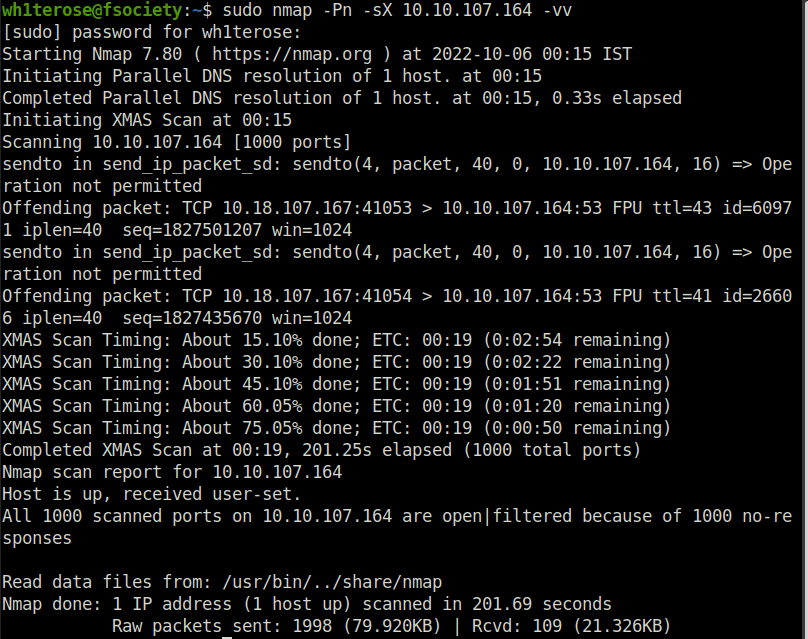
999
Question 3 – There is a reason given for this — what is it?
Note: The answer will be in your scan results. Think carefully about which switches to use — and read the hint before asking for help!
No Response
Question 4 – Perform a TCP SYN scan on the first 5000 ports of the target — how many ports are shown to be open?
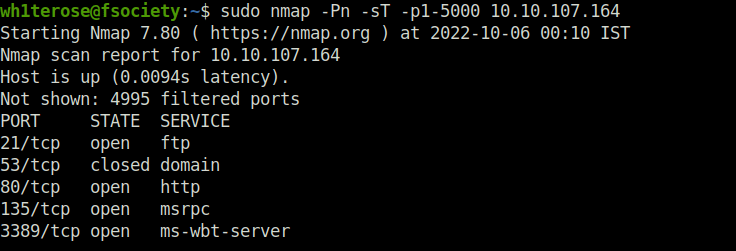
5
Question 5 – Open Wireshark (see Cryillic’s Wireshark Room for instructions) and perform a TCP Connect scan against port 80 on the target, monitoring the results. Make sure you understand what’s going on.
No answer needed
Question 6 – Deploy the ftp-anon script against the box. Can Nmap login successfully to the FTP server on port 21? (Y/N)
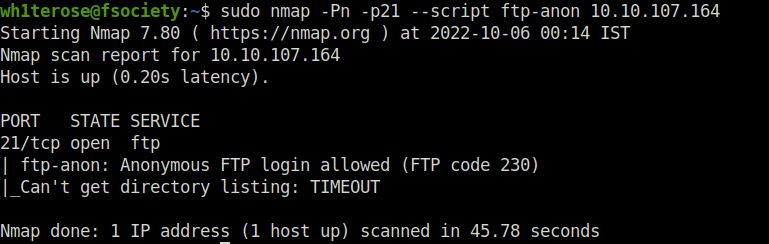
Y
Task 15 – Conclusion

Also Read: Hacking social media accounts with Zphisher

So that was all, from now on, you are ready to scan those machines out there, check live hosts in the network, find open ports on those live hosts, find the service version running for further enumeration. Firing up the NSE scripts to find the exploitable vulnerabilities. Nmap is a great tool to keep in your arsenal, I will be covering more detailed articles and tutorials on this all-in-one network pentesting tool, till then “Happy Hacking”.




