In this walk through, we will be going through the OhSINT room from Tryhackme. This room consist of an OSINT challenge where we will use open source intelligence techniques to unravel information about a person. So, let’s get started without any delay.
Task 1 – OhSINT
Question 1 – What is this users avatar of?
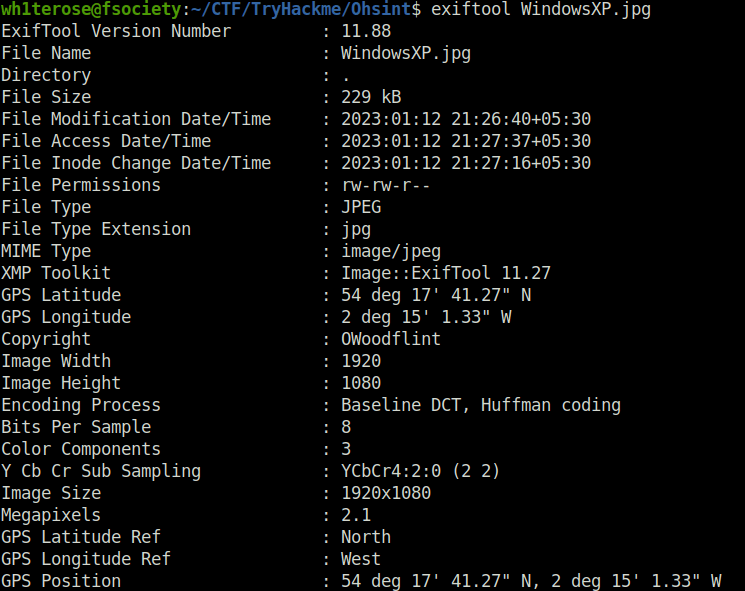
- Running exiftool on the image gives us the copyright holder name – OWoodflint.
exiftool WindowsXP.jpg
- Searching that name on Google, reveals the user’s blog, github and twitter. User’s twitter profile is of a cat. Hence, getting our first flag.
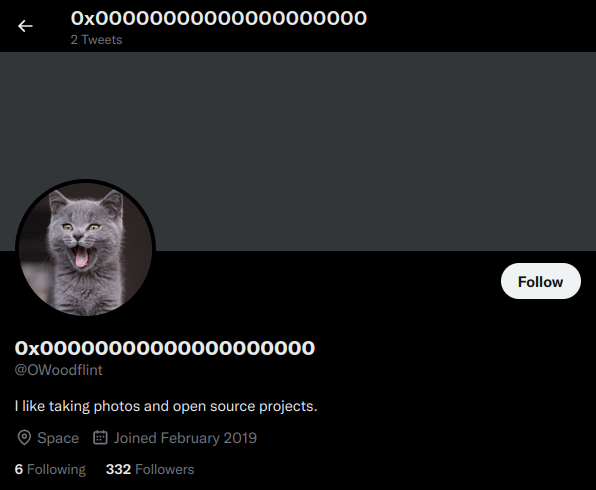
catQuestion 2 – What city is this person in?
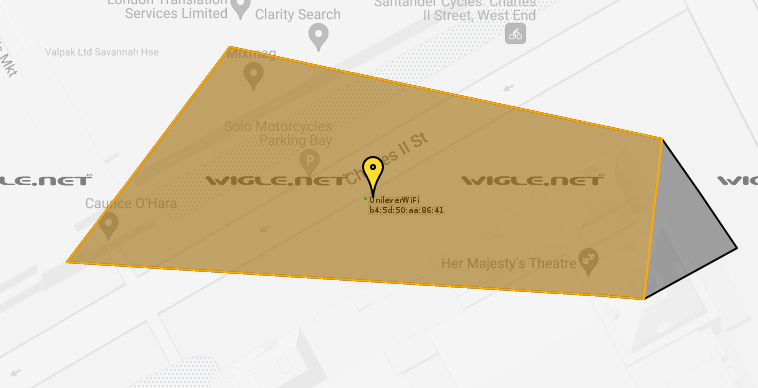
LondonQuestion 3 – Whats the SSID of the WAP he connected to?
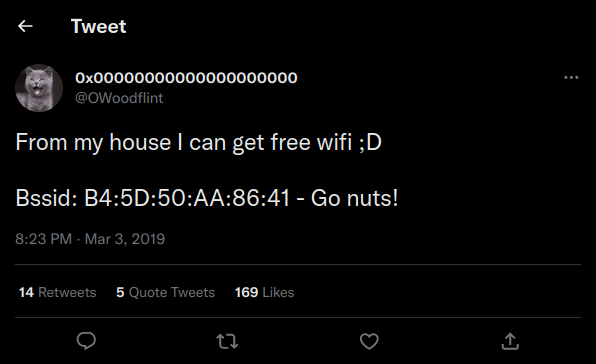
- We get the BSSID from one of the user’s tweets.
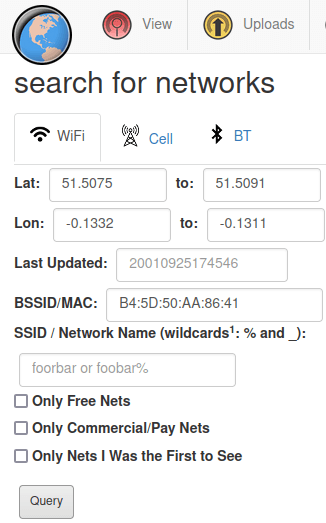
- Searching this BSSID on wigle.net gives us the location and name of the SSID.
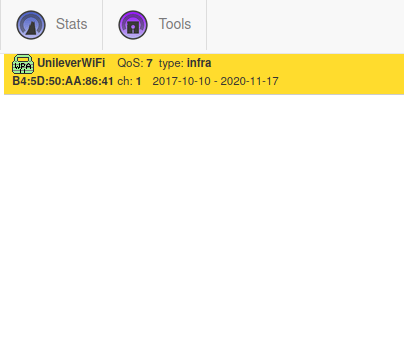
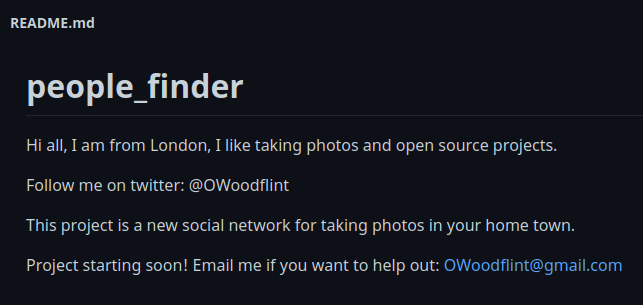
UnileverwifiQuestion 4 – What is his personal email address?
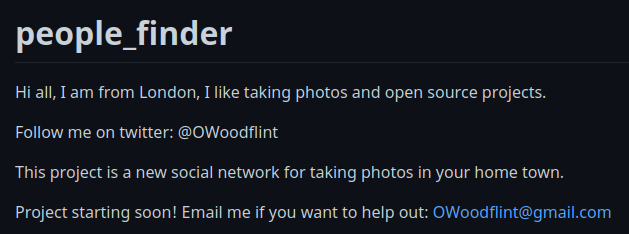
[email protected]Question 5 – What site did you find his email address on?
GithubQuestion 6 – Where has he gone on holiday?
- Getting this info on the Oliver Woodflint wordpress blog found earlier.
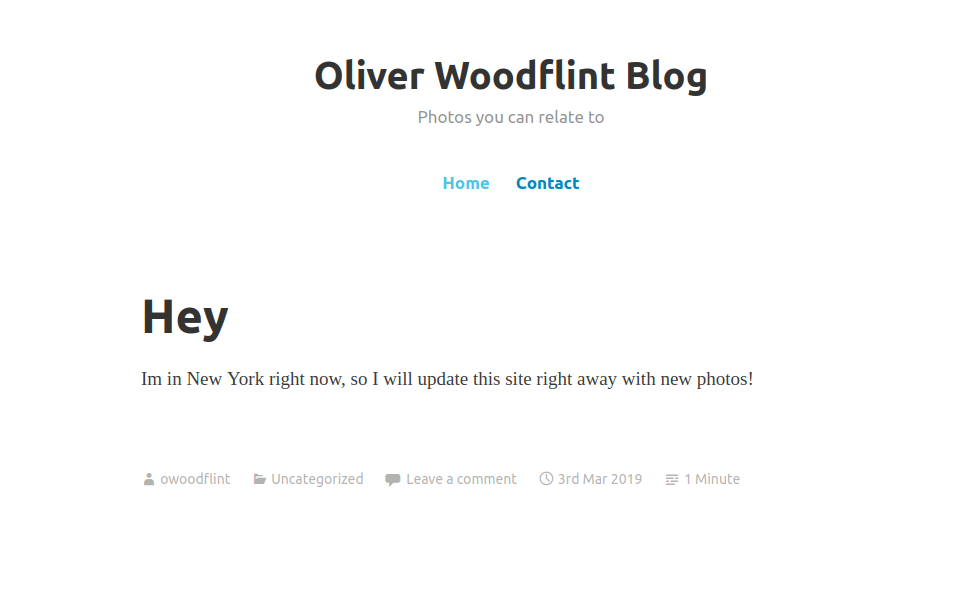
New YorkQuestion 7 – What is this persons password?
- Finding user’s password in his blog source code. I tried looking into before too by Ctrl + F “password” however left it untouched. Then waste some time in github commits.
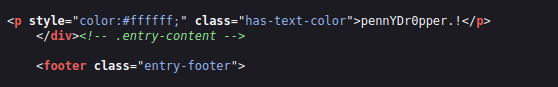
pennYDr0pper.!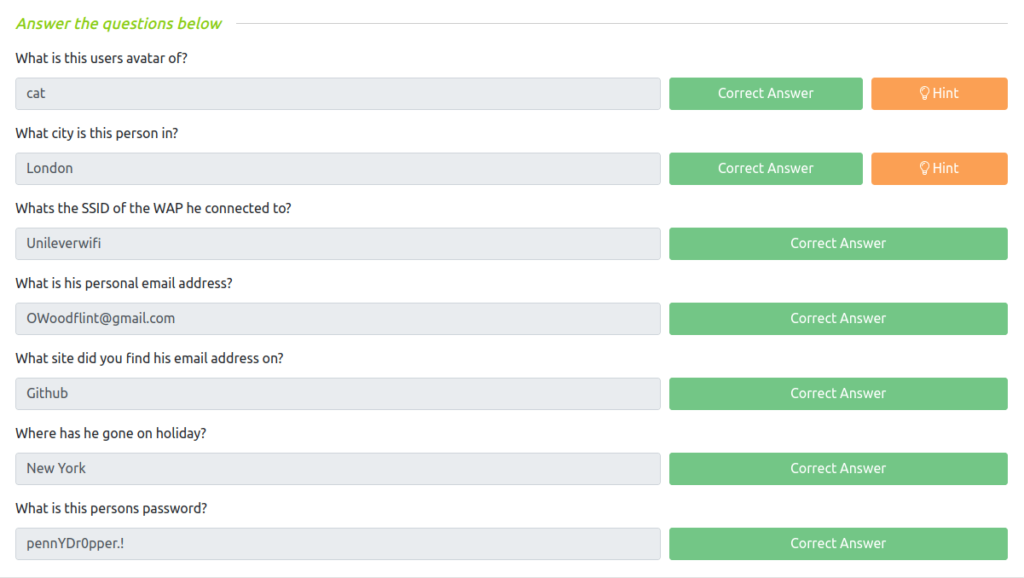
Also Read: Tryhackme – Nessus
So that was “OhSINT” for you. In this room, we have covered an OSINT challenge where we uses Open Source Intelligence techniques like exif data analysis, Social media enumeration, Wifi AP investigation and more. In Short, it is an easy and fun room to practice your OSINT skills. On that note, i will take your leave and will meet you in next one. Till then, “Keep Hacking”.




