In this walk through, we will be going through the Broken Authentication (Weak Passwords) vulnerability section from bWAPP Labs. We will be exploring and exploiting Weak Passwords in application and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.
Table of Contents
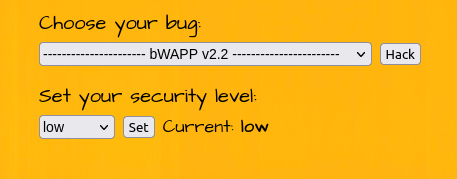
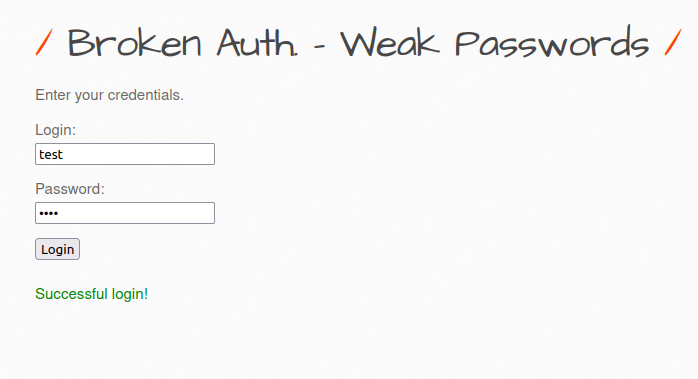
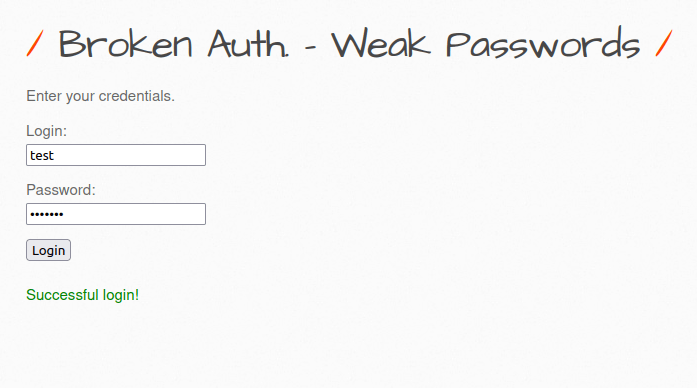
Security: Low
- Setting the security level to Low.
- The application has an authentication mechanism and ask for pair of credentials to login. It issues a POST request to ba_weak_pwd.php file for further execution.
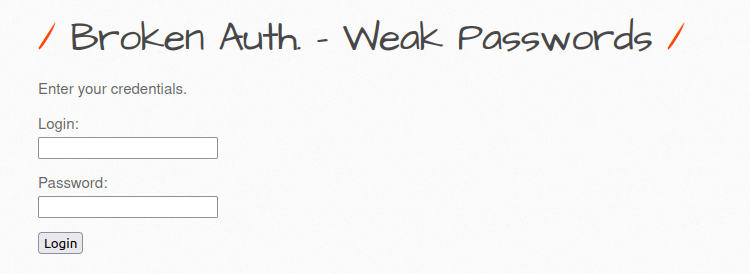
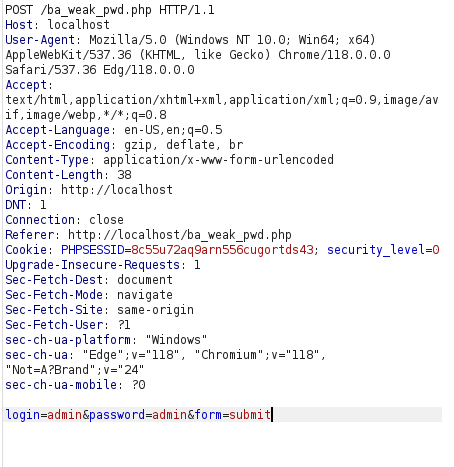
- As the challenge is related to weak passwords, i used the below set of credentials and got a successful login on test:test.
admin:admin admin:password test:test
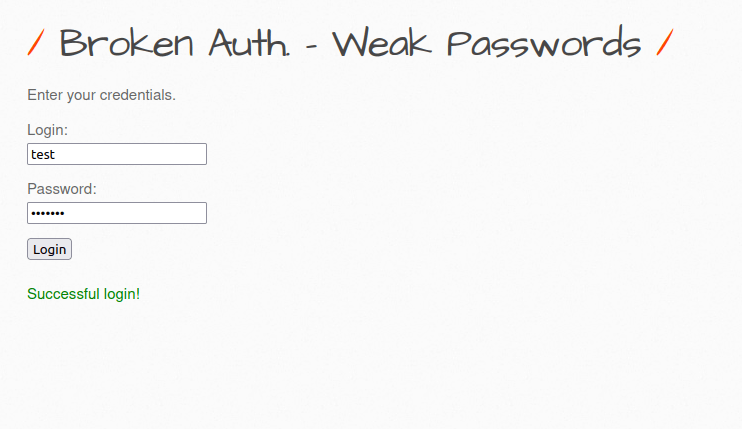
Security: Medium
- Setting the security level to Medium.
- I used the below set of credentials and got in successfully.
test:test123
Security: High
- Setting the security level to High.
- I used the below set of credentials and got in successfully.
test:Test123
Also Read: bWAPP – Broken Authentication (Logout Management)
Conclusion:

So, we finally completed all the security levels for the bWAPP Broken Authentication (Weak Passwords) Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Next, we can mitigate the potential weak password attacks by implementing a strong password policy and avoiding default or commonly used password. Along with that, a lockout mechanism on the login panel will be beneficial in case of bruteforce attacks. On that note, i will take your leave and will meet you in next one with another bWAPP vulnerability writeup, till then “Keep Hacking”.




