Hello and Welcome back, my aspiring hackers. How are you? Today, we will be learning, how we can be anonymous while hacking using the kali-whoami tool.
While hacking into target systems, one of the most important things, which most of the amateurs missed out on is the OPSEC. So, what is Opsec?
OPSEC stands for Operational Security. It is the process that an individual or organization deploys in order to maintain anonymity during an operation and it involves the prevention of sensitive information from getting into the wrong hands. It was usually associated with spies back then in the Cold war era, but it is relevant more than ever today in this digital age. Today with the advancement of technology and with the increase of more devices in our lives, Hackers don’t have to work hard too much. So hacking is one thing, and covering your ass is another thing. I truly stand up for OPSEC and the very necessity of it, while hacking. Now you understand what OPSEC is, let’s start with the tutorial.

What is kali-whoami?
Kali-whoami is a tool by which you can be anonymous while hacking in your Kali Linux. It has various options and features that we can implement in order to be anonymous. The features are as follows:
- Anti-MITM – It stops Man-in-the-middle attacks on your system.
- Log Killer – Deletes all logs of your activity in your Kali Linux System.
- IP Changer – Change your IP in order to mask your identity.
- DNS Changer – Change your Domain Name System (DNS) to avoid DNS leaks.
- Mac Changer – Change or Spoof your Media Access Control (MAC) address, as it is the only identifier that is hardcoded into your system. It can be beneficial while using Public Wifi to not get uniquely identified.
- Time Zone Changer – Your Time Zone tells a lot about your activity and your working hours. This option will spoof your time and time zone in order to mask your true identity.
- Hostname Changer – This will change the hostname of your Kali Machine.
- Browser Anonymization – It will anonymize your searches by using TOR.
- Anti-Cold Boot – This prevents Cold Boot attacks from happening on your hard disk.
Note – These are all the options, provided by the tool but some of them may or may not work in your system. The working of all the options will be presented to you in a moment.
How to be anonymous using the kali-whoami tool?
Step 1 – Download and Install the Kali-Whoami tool.
Fire up your Kali Linux and go to the following link: https://github.com/omer-dogan/kali-whoami
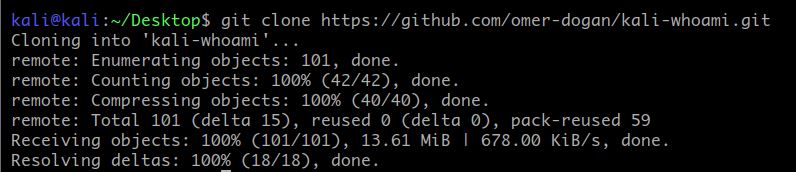
Copy the following link and open up a terminal. Next enter the following command to git clone the repository in your system.
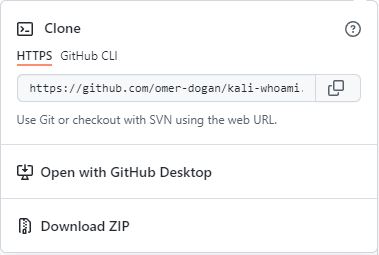
git clone https://github.com/omer-dogan/kali-whoami
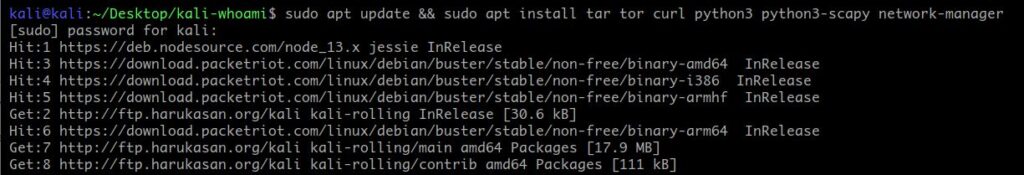
Next type the following command to update and install all the necessary packages for the tool. Please be patient as this might take a while, depending on your internet speed.
sudo apt update && sudo apt install tar tor curl python3 python3-scapy network-manager
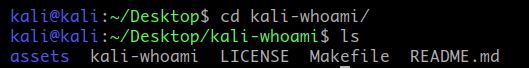
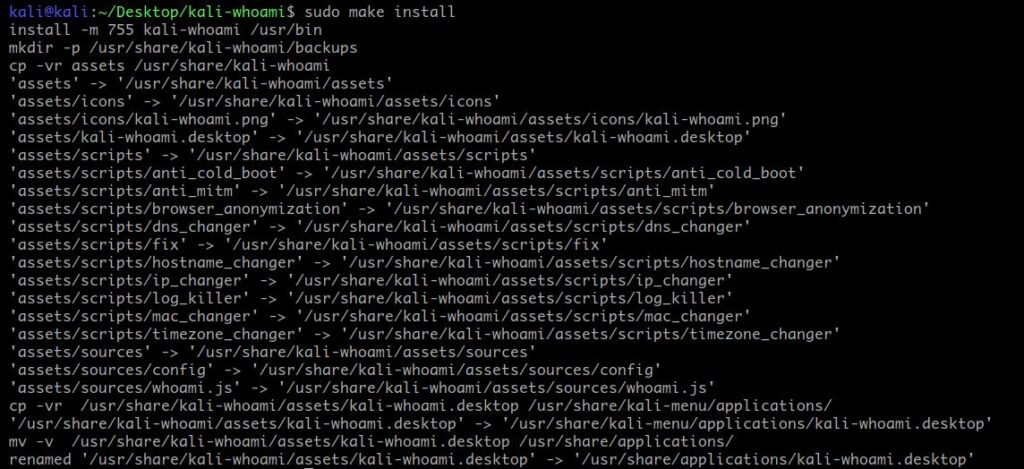
Now navigate to your kali-whoami folder and type the following command in order to install the tool. For that first “cd” into the folder and then type the following command.
cd kali-whoami sudo make install
Step 2 – Learning how to use the tool.
Now type the following command to get the tool working.
- Kali-Whoami Help – Type the following command to see the help of the tool. This will list all the options related to the tool.
sudo kali-whoami --help
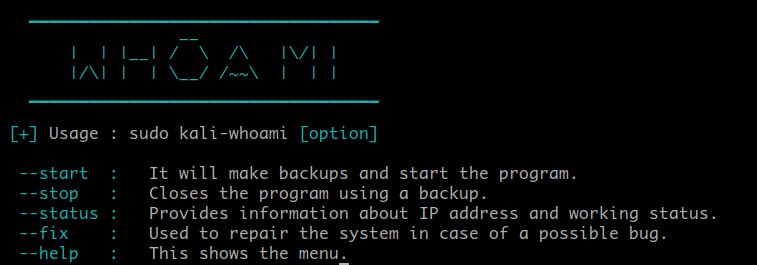
- Kali-Whoami Start – Type the following command to start the tool.
sudo kali-whoami --start

Once the tool is up running, you will be greeted with the above-mentioned interface. Now to select all the options one by one. Type 1 to 9 and press “Enter” after each option for enabling it. Once this is done, press Enter one more time and it will show you the options that are working and that is not on your system. Mine you can see in the attached picture down below.
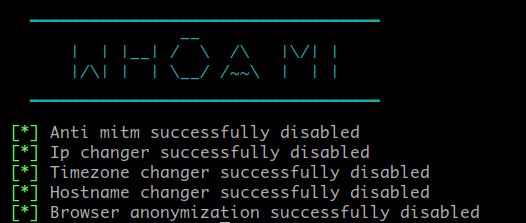
- Kali-Whoami Status – Type the following command to check the status of the tool and the features that are working on your system.
sudo kali-whoami --status

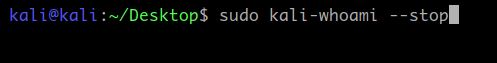
- Kali-Whoami Stop – This will stop all the services running related to this tool. Type the following command to stop the tool from working.
sudo kali-whoami --stop
Step 3 – Testing the tool.
We will check, how the tool is performing with respect to the enabled options. We will test all the options, if possible. I will be testing only those options, which are showing “enable” in my status menu.
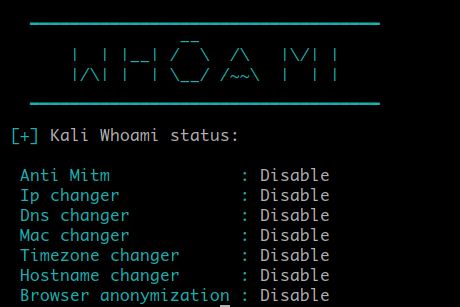
Test 1 – IP Change Test
We will be checking if our IP address has changed or not. For that go to your browser and type “What is my IP?”. This will show you your IP Address. I know, mine is already changed. You can check the location of your IP by clicking on any IP checking website from the result.
The result I got was great, It is showing my location in the Netherlands based on my IP Address, which is definitely not true. It is using TOR protocol to anonymize your IP Address. TOR is a great tool but it is slow.
Note – You will be forced to solve captchas before proceeding as google doesn’t like the use of TOR much. Solve a few of them, then you are good to go. In my opinion, avoid the use of the google, use search engines like duck duck go.
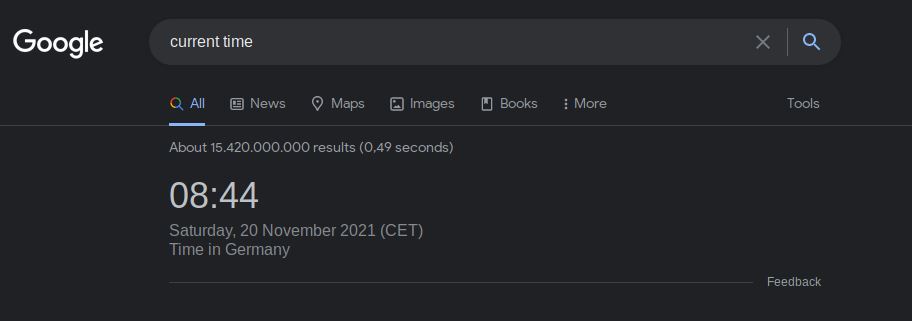
Test 2 – Time Zone Changer Test
I will not complicate this one, for this test, just go to your favorite browser and type “current time”. This will show you the current time based on your location, mine is showing Germany and the time zone is in CET, which is definitely not true.
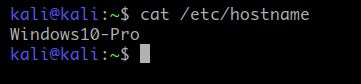
Test 3 – Hostname Change Test
To check the hostname of your system. Type the following command to check. Mine is showing Windows 10 Pro, which is a success.
cat /etc/hostname
Test 4 – Browser Anonymization
As it is using TOR for all the browser and IP Anonymization, we can check it by navigating to the given address: https://check.torproject.org/
Those who don’t understand what TOR is. TOR stands for The Onion Router. In laymen’s terms, it is a protocol that encrypts all your traffic and bounces it to three random nodes around the world, in order to avoid detection and revelation of the origin of the traffic.
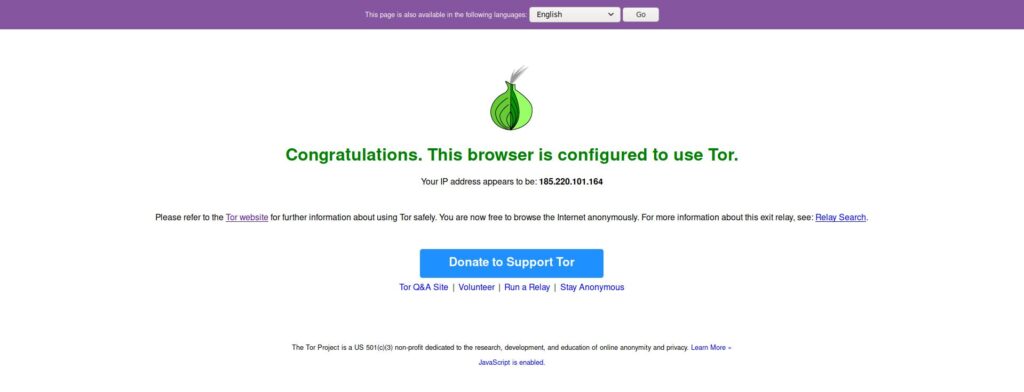
By checking the tor connection. We got success as it is showing, “Congratulations. This browser is configured to TOR.” If this shows red, then it is not good for you.
So we got all our results, we conduct 4 tests and we got a fair success rate. Talking about other options like DNS changer or MAC address Changer. DNS Changer doesn’t work and I think it is something from the tool end, not ours. Well, You can use encrypted DNS like using Cloudfare one (1.1.1.1) and if you are skeptical about your DNS test. You can perform a DNS leak test online. Next, the MAC changer doesn’t work on my system as I am running Kali on a virtual machine, your result may differ.
Taking about the overall performance, I think it can be improved as with the IP Change, we are located in the Netherlands but our time shows of Germany, I don’t know, was that a mistake or I am missing something. But my point is if your IP is showing you are based in the US right now, but your time zone shows of India, then it will not be a great opsec strategy as you will be uniquely identified between others and let me tell you that, if you are not on TOR, you can’t escape Browser Fingerprinting to the fullest. Well, that’s a topic of another time.
Also read: How do hackers get your exact location?
So, that is the Kali-Whoami tool that we use to our mask your identity and be anonymous while hacking, at least to some extent. Please, understand that No tool is foolproof and guarantees 100% anonymity. OPsec is something you have to practice as much you practice hacking. If you are using TOR and then logging into your personal Google account from it, then it is game over for you. So no personal information while operating on your freedom fighting missions. So, that’s all for today, this is Dolores Haze, signing off, till then “Happy Hacking”.



Like most tools on Kali Linux, “Kali-Whoami” doesn’t deliver. The IP, Time, and DNS Changer do not work. Albeit, the Host name Changer did. Overall, I always check my public address using kali@kali ~# echo $(curl -s https://api.ipify.org). Don’t bet your freedom on this tool…!