In this walk through, we will be going through the Buffer Overflow (Repeater) vulnerability section from Mutillidae Labs. We will be exploring and exploiting Buffer Overflow and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.

Table of Contents
Security Level: 0 (Hosed)
- Setting the security level to 0 or Hosed.
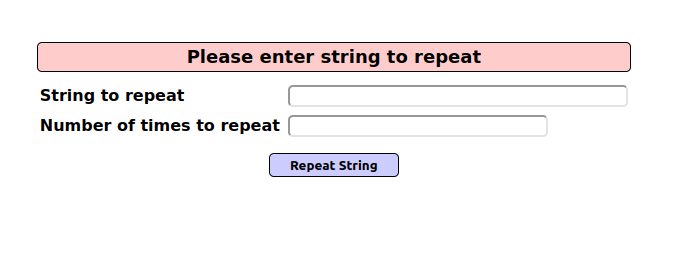
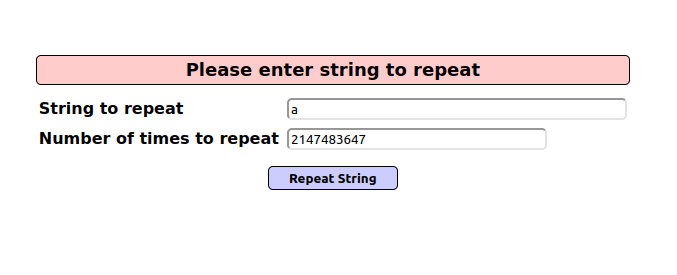
- The application has a input box to enter an string to repeat and the number of times we want it to repeat.
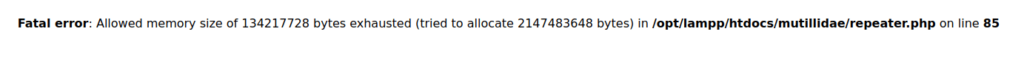
- I entered a very large amount of input in both the fields which causes an error in the application.
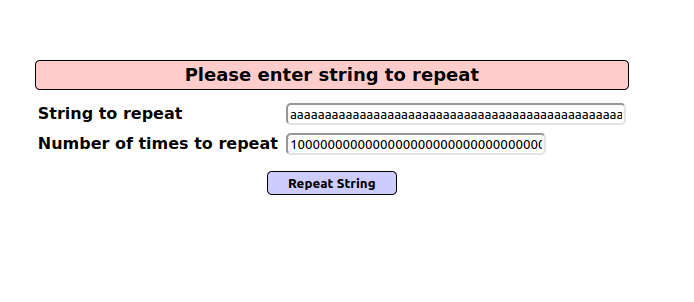

- I used the maximum specified amount this time and it still fails.
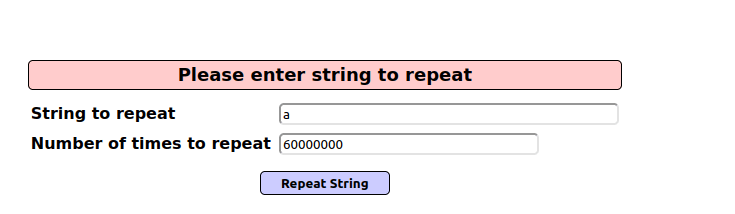
- Next, i bruteforce with the numbers of the repeat field and was able to halt the application processing for the maximum with the given number. Doing this 3-4 times will exhaust the application resource and a potential DOS will happen.
60000000
Also Read: Mutillidae – Blind SQL via Timing (Login)
Conclusion:

So, we finally completed all the security levels for the Buffer Overflow (Repeater) Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Next, we can mitigate the potential Buffer Overflow attacks by using Address space randomization (ASLR), Data execution prevention (DEP) and Structured exception handler overwrite protection (SEHOP) that will prevent malicious code execution on the target. On that note, i will take your leave and will meet you in next one with another Mutillidae vulnerability writeup, till then “Keep Hacking”.