In this walk through, we will be going through the Cascading Style Injection (Set Background Color) vulnerability section from Mutillidae Labs. We will be exploring and exploiting CSS Injection in Set Background color utility and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.

Table of Contents
Security Level: 0 (Hosed)
- Setting the security level to 0 or Hosed.

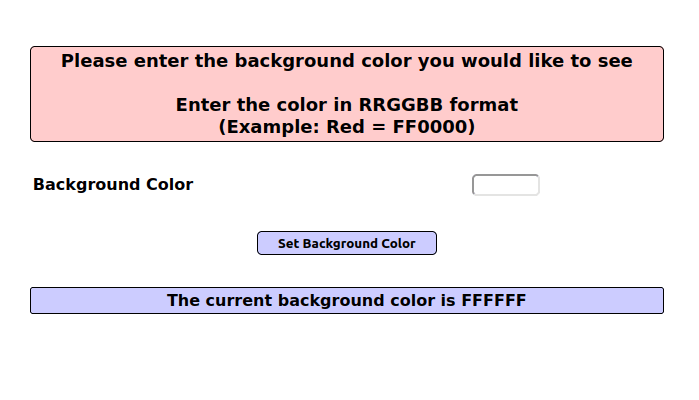
- The application has a set background color functionality which uses CSS and requires a color code in Hex to set it in the background of container. Below that it also shows the current color which has been set.
- I used the below payload to save our script in the current background color value. Whenever a user visit this page, the payload will be executed automatically and a pop-up will be generated.
<img src=x onerror=alert("Hacked")>;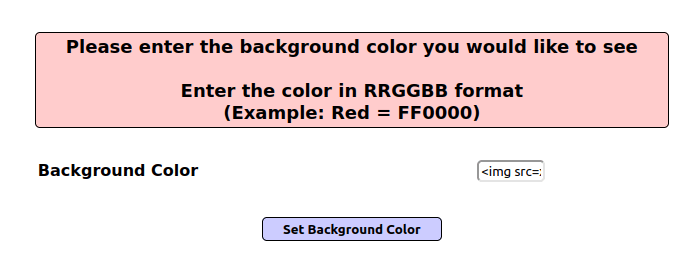

Also Read: Mutillidae – Blind SQL via Timing (User Lookup)
Conclusion:
So, we finally completed all the security levels for the Cascading Style Injection (Set Background Color) Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Next, we can mitigate the potential CSS Injection attacks by performing input sanitization and using CSP Header (Content-Security-Policy) which prevent browsers from executing malicious code on the website. On that note, i will take your leave and will meet you in next one with another Mutillidae vulnerability writeup, till then “Keep Hacking”.




