In this walk through, we will be going through the Google Dorking room from Tryhackme. In this room, we will be learning how Search Engines work and leveraging them into finding some hidden content. On that note, let’s get started.
Task 1 – Ye Ol’ Search Engine
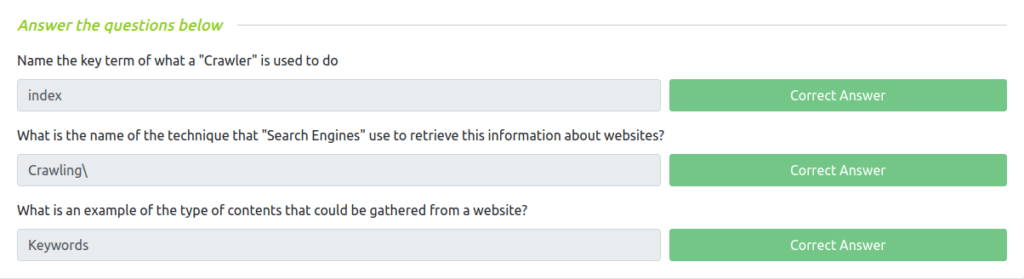
Task 2 – Let’s Learn About Crawlers
Question 1 – Name the key term of what a “Crawler” is used to do
index
Question 2 – What is the name of the technique that “Search Engines” use to retrieve this information about websites?
Crawling
Question 3 – What is an example of the type of contents that could be gathered from a website?
Keywords
Task 3 – Enter: Search Engine Optimisation
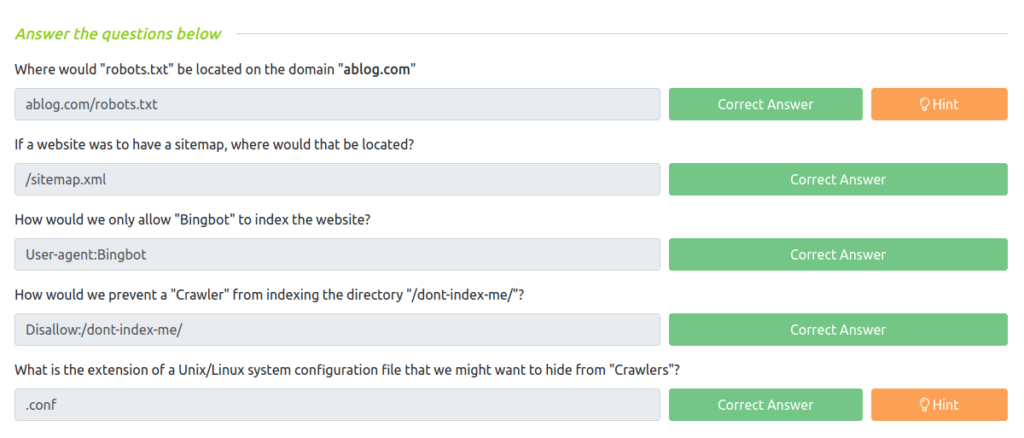
Task 4 – Beepboop – Robots.txt
Question 1 – Where would “robots.txt” be located on the domain “ablog.com“
ablog.com/robots.txt
Question 2 – If a website was to have a sitemap, where would that be located?
/sitemap.xml
Question 3 – How would we only allow “Bingbot” to index the website?
User-agent:Bingbot
Question 4 – How would we prevent a “Crawler” from indexing the directory “/dont-index-me/”?
Disallow:/dont-index-me/
Question 5 – What is the extension of a Unix/Linux system configuration file that we might want to hide from “Crawlers”?
.conf
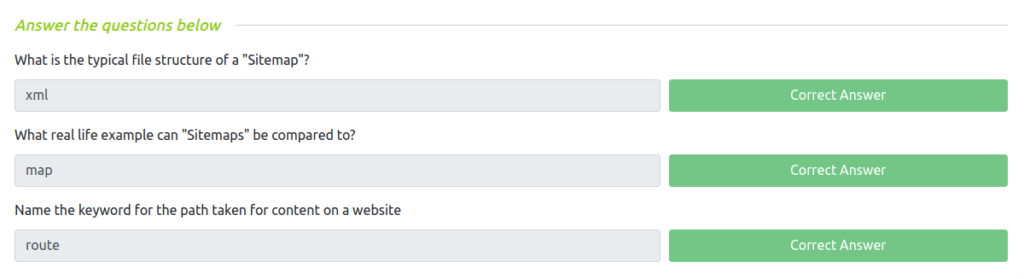
Task 5 – Sitemaps
Question 1 – What is the typical file structure of a “Sitemap”?
xml
Question 2 – What real life example can “Sitemaps” be compared to?
map
Question 3 – Name the keyword for the path taken for content on a website
route
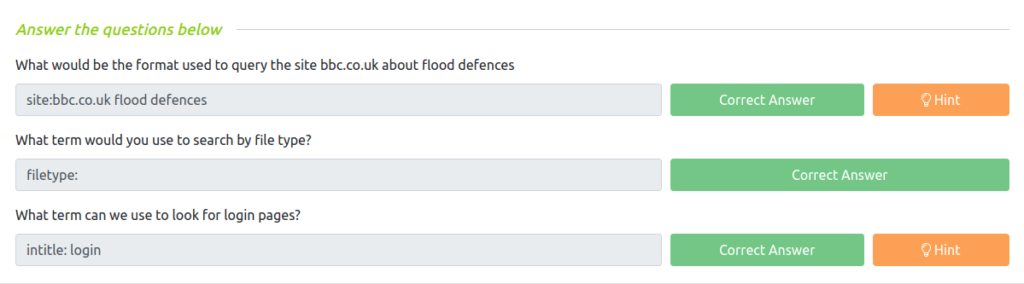
Task 6 – What is Google Dorking?
Question 1 – What would be the format used to query the site bbc.co.uk about flood defences
site:bbc.co.uk flood defences
Question 2 – What term would you use to search by file type?
filetype:
Question 3 – What term can we use to look for login pages?
intitle: login
Also Read: Tryhackme – Encryption: Crypto 101
So that was the “Google Dorking” room for you. Googling with the help of dorks makes the search engine reconnaissance easier on the target. In this room, we learned about the crawlers, sitemap, Search Engine Optimization, etc. Practice some more dorks from Exploit DB to identify some useful and juicy information enclosed on the web. On that note, i will take your leave and will meet you in next one. Till then, “Keep Hacking”.