In this walk through, we will be going through the Shodan.io room from Tryhackme. In this room, we will learn about the IOT Search Engine – Shodan.io and its usage to perform enumeration of the target devices. So, let’s get started without any delay.
Table of Contents
Task 1 – Introduction
Question 1 – Go to Shodan.io
Done
Task 2 – Filters
Question 1 – How do we find Eternal Blue exploits on Shodan?
vuln:ms17-010
Task 3 – Google & Filtering
Question 1 – What is the top operating system for MYSQL servers in Google’s ASN?
asn:AS15169 product:mysql
5.6.40-84.0-logQuestion 2 – What is the 2nd most popular country for MYSQL servers in Google’s ASN?
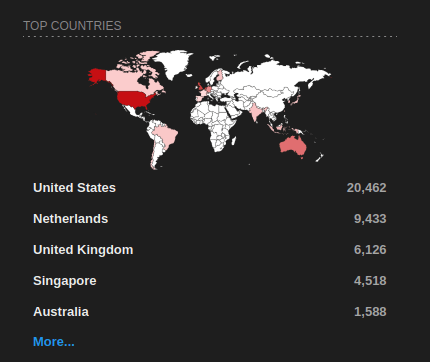
NetherlandsQuestion 3 – Under Google’s ASN, which is more popular for nginx, Hypertext Transfer Protocol or Hypertext Transfer Protocol with SSL?
asn:AS15169
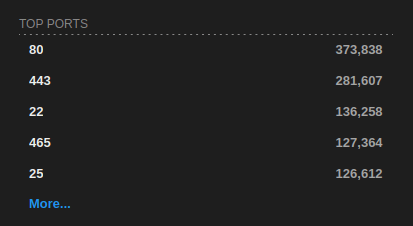
Hypertext Transfer Protocol
Question 4 – Under Google’s ASN, what is the most popular city?
asn:AS15169 country:"US"
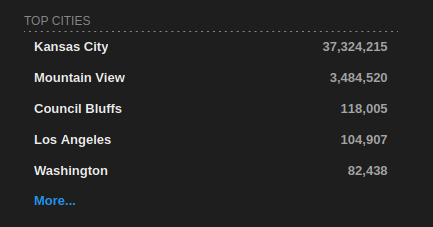
Kansas CityQuestion 5 – Under Google’s ASN in Los Angeles, what is the top operating system according to Shodan?
- Although the answer for this is Debian however things have changed since the room was created.
asn:AS15169 country:"US" city:"Los Angeles"
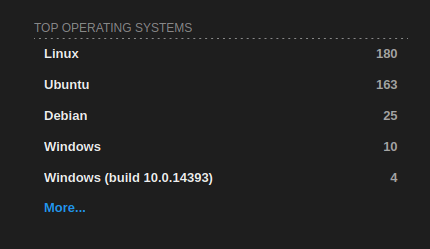
DebianQuestion 6 – Using the top Webcam search from the explore page, does Google’s ASN have any webcams? Yay / nay.
nay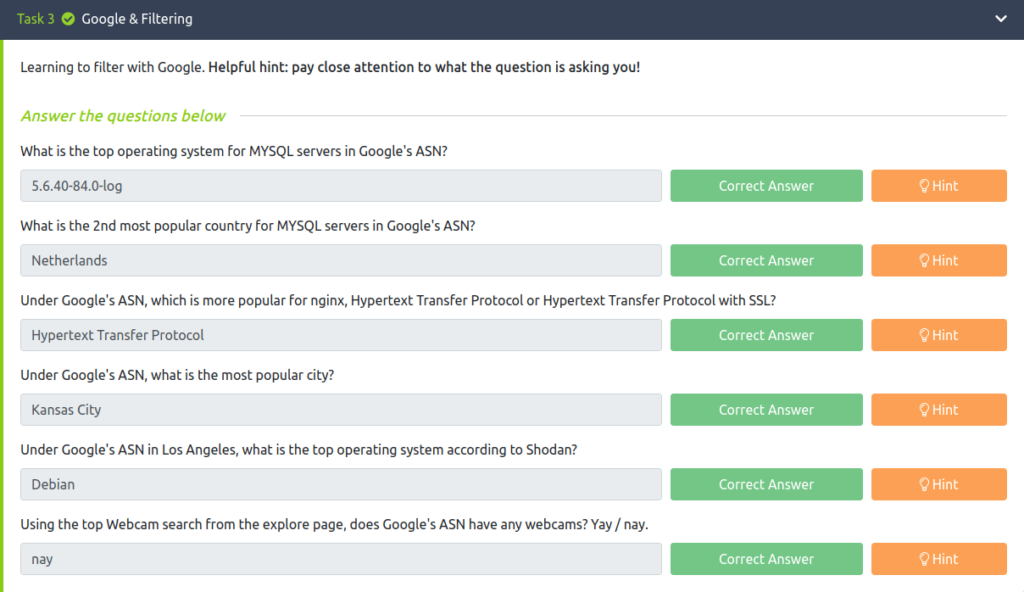
Task 4 – Shodan Monitor
Question 1 – What URL takes you to Shodan Monitor?
https://monitor.shodan.io/dashboard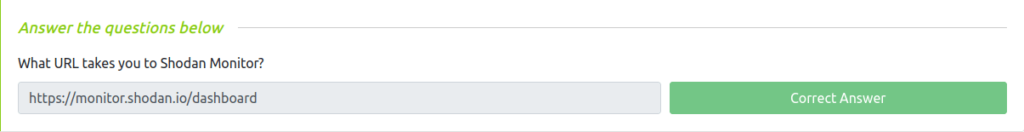
Task 5 – Shodan Dorking
Question 1 – What dork lets us find PCs infected by Ransomware?
has_screenshot:true encrypted attention 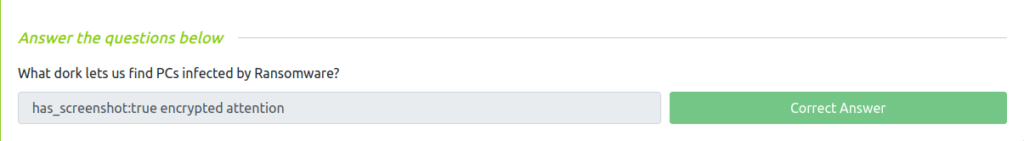
Task 6 – Shodan Extension
Question 1 – This will be nice for bug bounties!
Done
Task 7 – Exploring the API & Conclusion
Also Read: Tryhackme – Biohazard
So that was “Shodan.io” for you. We looked into the basics of Shodan and its usage. Next, we took a dive into Filters, Filering and enumeration and Shodan Monitor. At last, we learned about Shodan Dorking and Extension and concluded the room. On that note, i would take your leave and will meet you in next one. Till then, “Happy hacking”.




